by Herman Bailey | Mar 14, 2026 | Essays |
Introduction
The main objective of this research was t study cases of sexting among the teens. Due to the nature of behavior and the privacy concerned with the same, the study focused on teens who had been arrested by the police for engaging in such behavior. The focus was on understanding the prevalence of sexting, the risks involved and how teens responded tot any clinical measures that wren applied. Chalfen (258) begin by shoeing recent trends in sexting. The study may seem benign but the authors through the first paragraph quickly show the distress and the severance of the problem of texting. With the introduction of various technological aspects such as the freedom to use the internet, the fact that each teenager and in fact child owns a phone the prevalence of sexting has moved from adult circles to teens and children. The authors highlight that averagely every child by the age of 10 owns a cell phone which has unlimited access to the intent. Further, majority of the adults do not monitor what the child does with the phone. They give an example of a study conducted by Ringrose et al.(210) which found that more than 96% of teens have been exposed to sexting, and of this population more than 84% have continued to engage in sexting so that it has led to more and more graphic messages over time. With more social media sites dedicated to sexting, sexual exposure and pornography it is therefore likely that every teenager is exposed to the same behavior which to many seems harmless even though it can lead to severe consequences such as is addressed in this study that is, arrest by the police and engagement with the justice system.
Methodology
Two matters were considered in the selection of the methodology: on the one hand, there are the limits that come with studying teens who are considered children. There are several ethical issues which include consent by parents and limits to what the researcher can ask the children and how they can engage with the children. Although the primary data would be more useful and in fact more insightful, it is clear that such limitation would not only lengthen the study, they would also limit the number of respondents. Secondly, the data being sought by the study seems to been centered more on privacy. Sexting and engagement in any sexual behaviorism considered a highly private matter. Few if any of the teens that have been sampled for the study would be willing to engage with the researcher on the same. It is n this basis that the researchers approached the study from the police and investigator’s view. The researchers sampled the investigators who have handled sexting as cases and mailed questionnaires with the required responses to them (260). Mailed questionnaires have several advantages that in themselves could have been attractive to this study. First, investigators rarely have time to sit through an interview, therefore the questionnaire allows them to structure and fit in the study into their own schedule. Secondly, some of the questions would require a look into case files which are not only confidential but also need time to recall. The mailed questionnaire allows the investigator to maintain confidentiality and not divulge unnecessary information thereby ensuring protection of the subjects being studied and maintaining ethical principles of research.
Results of the study
Definition of sexting: according to Chalfen (262) sexting in this study was not limited to the sending of explicit messages whether coded or otherwise, but also the sending of sexually provocative images and production of the same. Before an image is sent, there must be a process of production that is the posing and taking of the picture to be sent. This entire process as highlighted through the study culminates in setxing. Teens not only send explicit message, they are also involved in production of the same messages. From the data gathered from the police officers, it is the images which often draw attention of investigators because majority of the images may not be taken through consent and where teens are involved are considered distribution of child pornography which in itself is illegal whether consent was involved or not.
Prevalence of sexting: more than 3,477 cases were reported to the police and investigated for producing and disseminating sexually explicit images. This is in comparison to data collected by the police departments involved in the previous year showing the cases to stand at slightly below 2000,Chalfen (262). The increase in sexting could be attributed to early exposure to sexuality among the teens and access to private mobile phones as well as free internet for purposes of sexting. With the resources being available, it is difficult to control the menace. Further, there has been an increase in investment by police and justice departments in resources and technology that are directed at curbing the behavior which in turn means that culprits are easier to find and records are easier to maintain on the same issue.
Aggravating circumstances: the authors are quick to differentiate between normal sexting and sexting that is directed to aggravated behavior such as forcefully obtaining images and distribution of images without consent. The study found that two thirds of the cases reported involved aggravated behavior where the victims are more than likely to have reported such behavior. The reports came therefore not form constant monitoring but rather from the reports of victims who were caught in the sexting scandals and processes. Of these as shown in . Chalfen. (265) 36% involved an adult as the initiator of the behavior. Therefore, the teen either was coerced or forced to produce, send and disseminate sexually exploitative images of themselves or others by an adult. And 31% involved a minor as both the producer and victim of the sexting. From the study, it is clear to see that more and more teens are becoming producers often sending the same images as either acts of maliciousness or simple misdirection. This concurs with data gathered by Dake et al. (3) who also showed that more teens are engaged in sexting, a behavior that has led to many arrests and other risky behavior. In fact, in their study they found that few if any teens understood the risks of engaging in sexting. Majority were not even aware that they could be arrested or that there exists a law that prohibits distribution of sexually exploitative images until they were arrested. In 62% of the cases where an adult was involved arrest was made. However, the study also found that in 18% of the cases arrested, the youths were simply experimenting new ways to engage their own partners in sexuality.
Mode of distribution: there are various ways of distributing sexting images, including the use of computer through emailing and social media and the use of the mobile phone through sending messages and social media. With this in mind, the study found that from the data gathered 63% of the images were distributed by phone only. With more and more teens owning phones and technology having advanced so much that the phone can send and receive documents of all nature, it is not surprising that majority of the images were sent via phone. Henderson (9) concurs in his study indicating that, majority of the teens often feel that the use of the cell phone guarantees a form of privacy for both the receiver and the sender. In addition, the mobile phone is much easier to access and make use of at any time with much convenience thus making it an ideal tool for sexting. This, in addition to the fact that it is quite difficult to monitor the activity of a cell device without violating the rights of the individual involved.
Dissemination: the study further found that majority of the images (70%) that were sent did not reach the internet. This limited the distribution and viewing of such images. The senders seem to be aware of monitoring of internet images but lack the same for withal when it comes to the use of their own mobile phones. Police have applied resources in ensuring that sexually explicit images do not reach the internet. This also means that the individuals involved made use of private accounts rather than public social media sites to produce, manufacture and distribute the images involved.
Conclusions
The study was to just direct at gathering data but also highlighting the risks that are involved in sexting and one such risk that was the focus of this study was arrest. By making use of arrest records, the study allowed the readers to get an idea of the prevalence of sexting as a behavior and some of the ways in which the images are produced and disseminated. As seen in this study majority of the cases that come to the attention of the police pose a form of risk healthiest and emotionally to those involved. This could include exposure to abuse and psychological manipulation. Majority of these cases involve an adult and a minor who is unaware of the risk that they are exposing themselves to.
However, there are some cases where the behavior involved was quite being. Where such cases were reported, scare tactics were used to discourage the building up of such behavior including, arrest, slight interrogation and lockup for a few hours. It is important to note that few offenders of the being nature were arrested again; most were reformed by the simple scare they got from the brush with the law.
Overall, the study found that arrest is not typical where adults are not involved. This supported the conclusions found by Wolak et al. (5) who indicated that cases where adults are not involved are often considered benign and built on youthful negligence, experimentation and poor judgment. They are therefore not taken as seriously, and as such rarely investigated deeply or with the aim of ensuring an arrest and conviction for malicious intent or breaking of the law.
References
Chalfen, R. (2009). ‘It’s only a picture’: Sexting,‘smutty’snapshots and felony charges. Visual Studies, 24(3), 258-268.
Dake, Joseph A., et al. “Prevalence and correlates of sexting behavior in adolescents.” American Journal of Sexuality Education 7.1 (2012): 1-15.
Henderson, L. (2011). Sexting and sexual relationships among teens and young adults. McNair Scholars Research Journal, 7(1), 9.
Ringrose, Jessica, and Laura Harvey. “Boobs, back-off, six packs and bits: Mediated body parts, gendered reward, and sexual shame in teens’ sexting images.” Continuum 29.2 (2015): 205-217.
Wolak, Janis, David Finkelhor, and Kimberly J. Mitchell. “How often are teens arrested for sexting? Data from a national sample of police cases.” Pediatrics (2011): peds-2011.
With a student-centered approach, I create engaging and informative blog posts that tackle relevant topics for students. My content aims to equip students with the knowledge and tools they need to succeed academically and beyond.
by Herman Bailey | Feb 25, 2026 | Essays |
The essay argues that text messaging has many advantages compared to phone calls and will argue in support of text messaging with relevant examples. It is common to observe many young people especially the teenagers and the young adults prefer texting messages using their phones instead of making phone calls. This is because of relative advantages text messaging has over phone calls.
The first advantage of text messaging is that it is more discrete compared t phone conversation. Hence more ideal for a person who wants to communicate when they need not be heard. For example, in a group of people or in an office or in the house, person will prefer to send a text message so as to pass message when the people around are not aware of the content and to whom you have communicated with.
Another advantage t text messaging over phone calls is that it is a convenient way of communication to the hearing impaired people and the deaf. A deaf person can easily communicate with another person if he or she can read and text a message since they are unable to communicate verbally and listen. This makes text messaging advantageous compared to phone calls.
Text messaging is a store- and –forward service which means that when a person send a text message to another person be it a friend or a family member, the message does not go to the receiver’s phone directly. The advantage of this service is that the receiver’s phone does not need to be in range or active for an individual to send a message. The message will be stored for some few days in SMSC until the receiver will turn on his or her mobile phone at which the message will be delivered at that point. His is unlike phone calls where a person needs to be active to receive the call, or be in range to receive it when they are offline, the receiver will not receive the phone call or when he or she I not near the ringing phone, they will not answer it. Similarly, the text message will remain in the receiver’s Sim card or in the phone until the time he or she will delete it. This is unlike phone calls where you could not trace a conversation after the end of the phone call if it was not recorded.
Another advantage of text messaging compared to phone calls is that text messaging can be used in sending similar messages to a large group of people at a time especially from users of a particular area or from a contact list, and this process is referred to as broadcasting. For example, may companies especially the mobile phone companies and use text messaging service to send similar text messages over a large number of people at the same time from their contact lists. Similarly, many companies use text messaging in distributing news from the company and other relevant information to their subscribers. This is unlike phone calls where you anno call a large group of people with similar messages and is also cumbersome.
Text messaging does not overload networks compared to phone calls. For examples, many companies especially the TV shows and radio programs frequently use text messaging to engage their listeners and also let their viewers and listeners to make a contribution on a topic or even vote in a poll topic.
Lastly, a person can subscribe to get a test messaging on services such as weather alerts, medication reminders, news headlines, movie showtimes, driving directions, traffic updates, and local business listings. These services are not offered by phone calls hence texting is advantageous.
In conclusion, from the example essay text messaging has many advantages compared to phone calls since it is more discrete, it is convenient for the deaf,, it stores information, can be used for large number of people, does not overload network and offer subscription services.
With a student-centered approach, I create engaging and informative blog posts that tackle relevant topics for students. My content aims to equip students with the knowledge and tools they need to succeed academically and beyond.
by Herman Bailey | Jan 26, 2026 | Essays |
BACKGROUND OF THE PROBLEM
Project plans are used to guide the project from initiation all the way to closure. In the past, more focus was given to the actual implementation of the project. There was little attention is any directed at planning before takeoff. The result is that majority of the projects by organizations were established haphazardly and lacked the proper sustainability. In the end, failure was imminent. Through research and various studies, the importance of project planning was understood.
Today, many NGOs seek professionals to plan their projects. In essence the organizations themselves posses the dream that is what they would like to accomplish through their projects but lack the way to make such dreams a reality. The planners offer a bridge from the dream into reality. They establish the project goals and objectives and translate the same into workable tasks with responsibilities. Though some of the responsibilities of the planner fall into the category of a project manager during the planning stage, they are completely dedicated to planning and reviewing.
It has been noted that despite the importance of the planner, few have the necessary skills to organization, trouble shoot and manage the challenges associated with planning. This can be attributed to the lack of information with regard to proper and quality planning. Most of the information focuses on management of the project and completely neglects planning. Planning information is often in the footnote or hidden among the massive information on management. It is therefore not surprising that planners are unable to produce quality, workable and achievable plans which meet the expectations of the organizations.
STATEMENT OF THE PROBLEM
Project planning is the backbone of the entire project. Success and failure of the project rely heavily on the plan which must some together properly to deliver quality. Planners are tasked with the responsibility of taking the dream and turning it is not a reality. The process of planning includes the use of various methods and even strategies. However, planners often encounter various challenges that threaten the entire plan. Without addressing these challenges properly and exhaustively, the plan put forward for the project often lacks quality and integrity. Whereas some of the challenges may seem like large obstacles, resolving them is also quite easy and may require only a little more effort.
EVIDENCE OF THE PROBLEM
Recently focus has been drawn to various stagnated projects by NGOs. Though the initial expected outcomes of the project was one that could have led to increased development, more and more projects are failing to meet this objective. After much research, organizations have to the conclusion that majority of the projects fail due to lack of proper planning. Planners are unable to produce quality plans to guide the projects from initiation to closure.
THE CHALLENGE OF PLANNING FOR PROJECTS
ALLOCATING AND SCHEDULING
The most difficult step in planning is the allocation of time and estimation of budgets. Often planners find that time allocated to the project is not sufficient and the budgets are not factual. There are more proposals and activities than there are resources and time in every project. The ideal situation is one in which a proper balance is achieved between the activities and resources. Planners require a priority system through which they can determine activities with the biggest pay off and therefore focus available resources on the same. Planners are often dealing with little information on the type and general challenges that the project maybe facing. The tools employed in the early stages of allocation and estimation may therefore fail when tested in the field.
Up to now in the project planning phase, the sequence of activities is based solely on the technical or logical considerations. This means that the sequential activity cannot be completed up to and until the previous activity is completed. The plans at this stage assess that resources such as people and materials are available for the completion of the activities. In many cases however, upon implementation of the plan this is found not to be true, (Lewis 1995). A project planner may assume that adequate resources are available or will be available for the activities and therefore schedule parallel activities. However these activities hold the possibility of resource conflicts arising. The interrelationships and interactions among the time and resource conflicts are too complex in nature and solution. Often project mangers learn of this difficulty when it is too late and solutions are unavailable. A deficit of resources alters the goals and even the quality of the project. Planners need to be careful to allocate the resources properly to ensure availability in the right quantities and din the right time.
The resource constraints often facing a project planner and for which he must find solutions include:
People: often called human resources and classified as per the skills and experience that they will bring into the project. The skills need to be exploited and properly utilized to ensure that the project moves on smoothly. Where human resources are not properly utilized losses and stagnation can easily besiege the project.
Materials: cover a very large spectrum dependent on the nature of the project. A majority of the delays in the project and stagnation of the same have been blamed on the scheduling of material delivery is now becoming a must in the plan.
Equipment: is usually presented in terms of type, size and quantity. Often planners overlook the availability of equipment as a constraint. The most common mistake is to assume that the available resource pool will be adequate for the project. However at the time of the project such resource pools maybe occupied.
The Scheduling Problem
Where scheduling is a problem planners are expected to classify the problem into either: time constrained problem and resource constrained problem. Haugan (2002) states that a time constrained project needs to be completed within a specific time and date. Time for this project is critical, failure is deemed as delay and wastage of exact resources. That being said, projects with resource constraints need to ensure that resource usage should be no more than is necessary and sufficient. A resource constrained project is one that assumes the resources available are completely sufficient for the completion and success of the project. Once the resources are deemed inadequate it becomes necessary to delay the project until when resources shall again be deemed sufficient. To resolve this problem, planners take into considerations a few basic rules in the planning stage:
Keep allocation and estimation separate: allocate resources based on the amount of time and money the NGO can reasonably spend to get project results. Estimates however need to come from the project plan. After both the allocations and estimates are prepared, ensure that the project can be affordable. Otherwise return to change the plan.
In estimating, avoid bias: bias means focusing attention in either one way or another. This means that it is easy for the planner to biased in terms of quality and cost of the services required to make the project a success. Instead, it is better to make an honest estimate based on the maret prices without exaggeration, than deal with gaps that arise from biasness.
In estimating, be as accurate as possible: in the planning stage, often the project planner lacks the information required to make a precise estimate. Instead of making an actual, factual singular amount; it is better to use range where time and costs are concerned. Ranges allow for delays in time and increase in cost.
Details: planners often fail to put as much information as possible in the schedule and budget. According to Melton (2008), it is wise to ensure that the schedule and budget are more than detailed. Each minute and dollar needs to be accounted for so that it is easy to follow through with the plan. Further, a detailed budget and schedule plays a major role in the monitoring of the project progress.
ENSURING QUALITY IN THE PLAN
Many planners focus more on ensuring that the job gets done whichever way it is to be done. Often the quality of the project takes back burner. However, when the job is not done right it is just not done. This leads to the organization losing in terms of money, resources, time and even money. Organizations end up having to re-work the plan or lose to competitor projects that planned right with quality in mind, (Klein 2008). Errors in a project plan are expensive in terms of resources and even the success of the project itself. If a plan includes quality right from the beginning the expected costs are much lower. During planning, it is important to note that a good blue print of the project costs much less than a bad blueprint. However, the price of a bad design and plan will definitely be felt in the future.
Many planners ignore the importance of accounting for errors in that plan. Even when considering quality it is important to note that quality does not mean perfect. A quality plan acknowledges the mistakes, makes correction and manages them properly. When managed properly, the errors do not compound and therefore affect the entire plan. The focus is on preventing or removing the mistakes completely.
Quality planning puts the focus on the process that is, improving how the project itself works. When the planner improves the processes it follows therefore that the project will function smarter. In such a plan, the project is completed in less time and money.
Defining Quality
The biggest challenge in defining quality is that majority of the people will tell you that not much time should be spend on planning but rather you should just take off and begin working. Many planners imagine that quality is expensive; however, this is not exactly true. In a project, errors and mistakes cost much more and may weigh heavily on the success of the project. Quality is defined by the value. The planner needs to understand why the project is being undertaken by the organization. Further, quality also goes ahead to define exactly which value is added to the organization by the project. Quality can be defined in one singular statement. Therefore, the project should indeed begin working from the beginning with the quality being the driving concept. According to Raz and Shenhar (2003), to ensure quality, project planners must:
- Collaborate not just with the organization for which the plan is being made but also the community who are recipients of the project. The plan needs to take the recipient’s view into consideration so that it remains relevant during the duration of the project.
- Continually remind the different stakeholders to keep focused on quality. There are times when teams are more focused on just completing a particular activity and less focused on how quality is measured for the same. Motivation for quality should be carried on through the different activities included at different stages of the project plan implementation.
- Plan for ideal communication channels. Most errors and delays in the project implementation can be attributed to poor understanding of the project plan itself. Stage after stage should include proper channels of communication to ensure that the message is well put and received by the recipients.
For some planners quality is an option. Sometimes they are more focused on making their project ideas and proposals the least expensive or doing the fastest jobs within the shortest schedules rather than delivering than actually delivering the best. The key to ensuring quality in a project is connecting the user benefits, that is, the benefits to the recipients to the technical functions that make the project work. Organizations are most likely to gain value and experience high quality when the tools being used are right for the job and every stage runs smoothly from the beginning to the end. Therefore planners design quality in from the top down, ensuring that they consider what adds value to the project recipients and then making sure that the project runs exactly as it is supposed to.
As each component is being structured and included in the planning of the project, test its features and functionality. As the entire project is coming together in the plan, it is also important to continually test the relationship of the various features, (Platje et al 1994). This ensures that each of the features continues to be reliable as well as valid in the project plan. The testing is done before the plan is implemented so that minor errors can be caught and dealt with before they become major errors. Without testing, planners increase the chances of letting errors slip through.
RIGHT PLANNING FOR THE RIGHT TEAM
A successful project is often defined as the rightly skilled people doing the right job. From this perspective the job of a project planner is to define the right job clearly, which ensures that organization can therefore reciprocate by finding the right people for the job. Once again the planner has the responsibility of keeping them focused on the job and removing any obstacles from their way. If all aspects of the project plan are under excellent control, people are facilitated to ensure team success which in turn translates to project success. The key for the right team is to combine an excellent team with a focus on proper goals for the project. Burke (1999) stipulates that Good teamwork reduces hassles, errors and keeps the human resource efficient. However, without the proper goals as set on the project plan teamwork is just fun that does not help to progress the project. The project plan provides the ideal focus so that the team proceeds with excellent work that has excellent results.
Getting The Right Team
In project planning, there are situations where the planner has no ability to select the team. In this case, the best that they can do is define the skills required for the completion of the task with as much detail as possible. This ensures that the implementers can therefore select the right people for the job. However, as is the custom today many organizations are opting to have the planners as part of the selection team. Project planners often play a key role in ensuring and making it possible to develop high performance project teams. They establish a team identity, create a common sense of purpose or shared vision and orchestrate decision making.
The process of selecting and recruiting project members will vary across organizations. The most important factors to consider for the planner are the importance of the project and the management structure of the project itself or the organization running the project. Lester (2003) insists that for high priority projects which critically determine the direction of the organization in the future, the project manager has the final say on whom they would like to be part of the team. For less significant projects, the planner and manager may require to convince the other branches of the organization on the importance of each individual to the success of the project.
In many project matrix structures, functional mangers control who is allowed into the project team. In such a case, it is ideal for the planner to work together with the functional manager in the selection of proper personnel. Experienced project planners often stress in their plans the importance of requesting and making use of volunteers, (Potts 2002). This means that the organizations give a chance to the employees to volunteer for the project. In this way a crucial balance between interest and skills can be reached, employees can be merited and an ideal team created for the project. When organization employees volunteer for the project, they complete the first step towards personal commitment in ensuring the success of the project. Such commitment as planners point out is essential in maintaining motivation when the project hits some hard times and extra effort from employees is required to pull out of the lag. For the planner there are less than obvious skills which are required in each step of the project and these include:
- Problem solving ability: If the project plan is complex and fuzzy, then it requires people who are excellent with creativity and posses the ability to work under uncertainty. This means that they can easily identify problems within the plan and find solutions for the same. They do not require a step by step guide in the plan but rather a general outline which guides the project.
- Availability: as any project planner indicates, sometime some of the most difficult things to predict in the plan is the availability of the ideal project team. Organizations may choose an ideal team which is overly committed and therefore bring little towards the success of the project. Planners require not just to state the ideal skills for the project but also the amount of time that such individuals require to ensure success of the project.
- Technological expertise: sometimes planners forget the importance of technological experts. This includes experts who can deal for example particular designs, machineries and other forms of technology. Unfortunately, these individuals may not be as available as imagined. This means that the plan should clearly state the skills required, for what importance and how such expertise will be applied.
In the corporate and NGO environment, the planner can seek audience with the HR managers who in turn fine tune the skills listed in the plan. This also gives the managers an opportunity to review the required skills and identify talent who can fill these positions.
Creating A Shared Vision
Project scope statements include specific costs, completion dates and performance requirements making them easy to define for the planners. On the other hand, the vision involves less tangible aspects of the same project and is much more difficult to draw. The vision provides a common image for the team on how the project will look upon completion. A poor vision has no clear definition of what the project is planning to create. The team therefore lacks a singular structure that brings them together, motivates them to work towards success of the project and highlight aspects of their success.
Majority of the planners often fail when they focus more on what the vision is rather than what it can accomplish. The vision can be captured in a slogan or even an image. Whatever it is does not really matter as much as what it seeks to bring together. A good vision gives members inspiration to give their best towards the project. The team includes various professionals, with different skills and backgrounds brought together by the vision which unites them, (Devaux 1999). Through the vision, project members are able to put down their individual agendas and come together to do what is best for the project. Visions also provide proper focus for the team members, giving them the opportunity to build upon the foundation in the decision making and selection process.
A good vision as generated in the planning of a project must include the following characteristics. First, the essential qualities of the vision should be able to be communicated. This means that the vision in itself should be clear and concise so that communicating to the team and other stake holders is an easy process which does not require any special skills. A vision is completely worthless, if the only person who understands it is the person who created it. Secondly, visions need to be challenging but in the banner of realism. A vision that lacks challenge often kills the motivation of the team at the early stages of implementation. On the other hand, if it is not realistic, it is not achievable and therefore also kills the morale of the team. Finally, a vision should be interesting enough to draw the right skills and talent to the project. People are not willing to put time and resources towards a vision that is boring and lacks interest.
Project planners often act as catalysts for the formation of the shared vision of a project team. The vision is designed to be inherent in the scope and objectives of the project. Even for the most mundane projects, planners face an array of opportunities through which they can create a compelling vision. Many visions evolve reactively in response to the situations on the ground. In some cases visions can arise informally. The planners take the time to collect the information on what the various stakeholders are interested in with regard to the project. They test bits of their working vision to gauge the level of excitement the early ideas elicit in others. Much has been written with regard to the role played by vision in the success of plans and projects as a whole. Some critics argue that the vision is just a glorified substitute for shared objectives. Others however, argue that it is one of the things that separates a successful project from the others. The key in a vision is to discover what excites the various stakeholders in a project, articulating the same source of excitement in the planning of the project and finally ensuring that this source is protected and nurtured throughout the plan of the project.
Defining Jobs Clearly Within The Plan
If an organization has team members who are willing to do the work, then the bulk of responsibility lies on the planner to ensure that they provide the right information that is the workers know exactly what they are supposed to do. At a minimum each singular worker required in the project should have clearly defined goals for each day they are linked to the project. In some cases, the planner may need to go beyond the goals and define the specific tasks that each worker will be undertaking. The key to making this work is being specific in the definition of tasks and the basic unit of work in the project. As planners, the task is to set up the job for someone else to complete. Rad and Anantatmula (2005), state that the task of the planner to ensure that all seven components of a task are put in place that is:
- Input: which are the terms and resources that go into the process and often end up as an output.
- Process: the actual steps and activities that the worker will do within the project.
- Output: this defines the product of the process, and includes the deadline and location of delivery.
- Tools: the planner defines everything that the worker will need to do the job properly.
- Techniques: here the planner sets forth the practical instructions for the sue process in addition to the skills required by the worker to complete the task successfully.
- Resources: the time spent and all other requirements which will be used up by the process and will therefore not be recycled.
- Work environment: this is the place where the project will take place. Dependent on the nature of the project, planners may provide insight into the physical terrain and even cultural dynamics of the setting of the project.
MAKING SURE THE JOB GETS DONE: PLANNING FOR RISKS TO THE PROJECT
Every planner understands that part of the process of planning is understanding the importance on anticipating and therefore planning for risks. Risk is defined as the inability to deal with, organize for and therefore manage chance events. The planner often has the difficult task of identifying and planning for various chance events that may affect the project. Vargas (2008) has been noted in majority of the cases planners are not equipped r skilled to plan for the unexpected. The process of planning for risks attempts to recognize and manage the potential and unforeseen troubles that may occur when the plan is put into action. The planner needs to identify as many trouble spots as possible (what could possibly go wrong), minimize the impact of the same (what can be done about the event in the plan), provide responses to those events in case they do occur (contingency plans) and provide for contingency funds to cover the risk events should they materialize.
The chances of a risk event occurring are greatest especially where it concerns an error in timing and cost estimates are greatest in the concept of planning. Conversely, the impact of the risk event can be minimized greatly through proper structuring and planning for the same. Planning for risks is a proactive approach rather than reactive. It is a preventive system that is designed to ensure that risks are reduced and negative effects associated with chance events are minimized. It gives the project better control over the future and can significantly improve the chances of reaching the project objectives and goals on time and within the budget.
The sources of project risks are many and mostly dependent on the nature of project that is being planned for. There are some sources which are from without the organizations such as the national political climate, the inflation rates and new laws set forth by the government. Such external events are vital to be considered in the planning stage before any organization can consider going ahead with the project.
Planning for risks begins by trying to generate a list of all the possible events that could jeopardize the project. Typically, the planner pulls together a risk assurance ad management team consisting of the relevant take holders. The team can help the planner through brainstorming and other problem identification methods to find and identify chance events within the project plan. One common mistake that planners often make is to focus more on the goals and objectives of the project rather than giving time to events that could in turn produce consequences whether positive or negative. Focusing on actual events ensures that it is possible to identify solutions for the same.
Risk Assessment
The first step in planning for the risk produces a list of potential events. However, not all the events require to be given attention at the planning stage. Providing attention to all the risks given could make the plan bulky, complex and confusing. Planners require to employ various methods to analyze the potential risks, eliminating those that seen inconsequential and organizing the worthy ones in terms of importance. Planners often asses the risks in terms of: probability and impact of the event. A main problem that faces the planners in this stage is biasness. Often planners are tempted to prioritize the scenarios for which they already have a solution to avoid work or even the probability of failure. The quality and credibility of the risk analysis requires that the planner defines each of the levels of risk and the probabilities of encountering the same, (Carmichael 2006). The likelihood of an event is completely different from the consequence of the same. Consequence needs to be the focus of risk assessment. Consequence in terms of the effect that may befall the project whether positive or negative from the risk.
Risk Response Planning
Once the risk is on the list, the next step is to determine what can be done to mitigate the risk. The planner commits to keeping the risk on track, and consequently doing something about the risk. The following are some the things that often provide a challenge in planning for a response to the risk:
- Mitigating the risk the information available to the planner may not be sufficient enough to plan for a proper and substantial response. There are two probable responses that is preventing the event altogether and reducing the impact of the event. In many cases, the planner often opts to reduce the impact of the same. However, even with strategies in place for mitigation it is likely that the risk will still pose a major problem to the project.
- In most cases in order to completely avoid the risk, the planner needs to alter the plans that have already been set. This means extra work, research, time and resources for the planner. In addition completely avoiding one event often translates to another risk taking its place.
- There are organizations that insist on avoiding risk through risk transference such as insurance. Unfortunately for the planner this may not be the most ideal of choices. Further, risk transference only covers very specific risks leaving the project open to others.
Planners often engage in planning for risks to compensate for the uncertainty inherent in project planning. Planning for risks reduces the number and impact of surprises and leads to a better understanding of the negative effects of some of the events. Contingency plans developed from risk analysis and planning often increase the chance that the projects will be completed in good time and within the stipulated budget of the organization, (Tomczyk 2005). Experience in project planning clearly indicates and shows that a formal, structured process to handle possible foreseen and unforeseen risk events will eventually minimize surprises, costs, delays, stress and even conflict. Planning for risk plays a major role in establishing and maintaining proper risk management throughout the project. Ultimately a successful risk identification and analysis in planning requires a culture where planners embrace threats rather than deny their existence; and also identify problems rather than hide them in the plan.
CONTINGENCY PLANNING
Because foreseen risks could easily become realities, planners need to come up with contingency plans. The contingency plan is drawn by the planner to mitigate the impact from the risk. The contingency plan is not part of the implementation plan. The contingency plan only comes to play when the project encounters the risk. When planners ignore the importance of a contingency plan, the project encounters a lot of delay and even risks of early closure before the outputs and products materialize. A contingency plan makes it easy to work around or with the problem so that delays and costs are managed properly.
One of the challenges encountered by planners when addressing contingency plans is the inability to decide the alternative path to be taken. When a risk is recognized as potential, planners come up with various solutions which can be used to address the same. Each of the solutions has its own advantages and disadvantages. The planners need to select the best alternative plan rather than prepare contingency plans for all the possible solutions. They make the decisions even though they may not be on the ground at the time when the project encounters the issue. They are however expected to find a solution that completely addresses the problem, maintains the budget and minimizes any delays.
The contingency plan often lacks the details that the implementation plan possesses. For this reason, there are organizations that do not see the importance of a contingency plan. Planners are therefore faced with the tough and difficult task of educating such organizations about the contingency plans and ensuring that they accept the contingency plan that they have drawn. According to Burton and Michael (1994), sometimes even when planners have taken the time to educate on the contingency plan, organizations still fail to implement the plan when the risk is encountered. Instead, they opt for trial and error methods of finding solutions. The result is an increase in cost and even time on the project. Where a proper solution is not found continued exposure to unnecessary risks often translates to complete failure of the project. For this reason, contingency plans should be addressed with the same seriousness and professionalism of the implementation plans. The plans should also address the what, why, who and how as in the implementation plans. As much detail should be given in the contingency plan to avoid miscommunication and half
PREVENTING SCOPE CREEP
Scope creep is defined as the addition of new pieces, goals and activities to the project after the plan has been completed. This is a major cause of delays, budget increments and ultimately failure of projects. When a project undergoes many changes, they compound and accumulate and in the end translate to scope creep. If a planner does not have a clearly written plan for the organization, it opens doors for anyone and anything to bring about major changes. A weak plan allows anyone who experiences challenges in implementing the plan to make their own changes. Majority of the reasons for scope creep are as a result of poor planning and communication of the plan to the team and stakeholders of the project.
Reason For Scope Creep
When stakeholders are not included in the planning stage of the project, they are often tempted to make their own additions to the plan and necessitate changes. Planners are often tempted to sit in their office and hammer out what they imagine to be the best plan without seeking the input of other stakeholders. When the plan is presented, however, everyone wants to make their own input which could in turn distort the plan completely.
The input from majority of the stakeholders should be sort not at the late stages or as a by the way, a practice that is common with planners but rather at the beginning of the planning. This ensures that their input is reflected in the plan from an early stage and avoids last minute changes which could translate into a bulk of work.
Sometimes, even with the best effort of the planners there often arises a misunderstanding on exactly what the organization is looking for or is seeking. This means that when such organizations see the plan, the end product of their project could differ greatly with what they wanted. The result is that major changes are required on the plan to meet the organization goals and demands, (Gaynor and Evanson 1992).
Finally, planners often ignore the importance of evaluating the situation on the ground before starting to plan. This ensures that the plan reflects current conditions and events surrounding the project. For example, the culture of the people may necessitate major changes in a project plan is the same is in conflict to ensure success. However, if the planner was aware of the situation and updated with the right information; the plan will reflect such culture and will not require a major overhaul. Regular evaluations and open communication channels are necessary to bring forth the right and best results in the project plan.
The project scope is the keystone that ensures all elements of the project plan come together in the most ideal way.
Defining The Project Scope
- Project objectives: the first step in defining the scope of the project is for the planner to come up with a general guiding objective. It is from this general objective that more specific objectives which guide the activities and the plan will be drawn. The project objectives help the planner to define the what, when and how of the project. Without a clear general objective, it is possible to lose focus and be steered in any direction.
- Deliverables: many times the planners ignore the outcomes or expected outcomes of the project until when the plan is completed. However, the outcomes should be defined at the beginning because they make it possible to make the plan as specific and the activities as directed as possible.
- Milestones: when planning, it is important to highlight events that are significant and that mark progress in a project. The deliverables often act as the right foundation from which the milestone schedule can be established and drawn. They occur naturally even during the planning stage and are easy for planners to recognize. Milestones often motivate those working on the plan and project because they establish growth and progress.
- Limitations: few planners understand the importance of limitations in defining the scope of the project. Limitations define the exclusions that the project will not be addressing. It may seem like an obvious aspect; however, without limitations stakeholders may not understand the boundaries of the project. When planners fail to define limitations, they open up the plan to false expectations and the [probability of expending resources on the wrong issues, (Bond 1996).
It is clear that scope creep can be reduced through a carefully structured scope statement. Although in a few cases, scope creep can have positive results; in majority of the situations scope creep results in added costs and possible delays in completion of the project. While planners are preparing to begin addressing the plan per se, it is important to be open about it so that stakeholders can bring in their contributions. Further, planners are tasked with the responsibility of investigating the situation that the project will be addressing thoroughly. From this investigation, they should draw a list of assumptions and address them in the plan. The result is that there will be very few surprises and/or reasons for change and demand for change.
MANAGING EXPECTATIONS
Planers often face the challenge that they may actually define the project correctly, prepare an exemplary plan with all the right information, and provide factual estimates and still end up with a plan which is a disaster. This is because the plan itself may not meet the expectations of the stakeholders and even the organization running the project. Organizations my not communicate their expectations openly or even in some cases communicate poorly. The result is that the planner may lack an understanding of the exact expectations of the organization. Though they labor continuously to work on a diligent project plan, the same is probably going to fail because it is not in line with the expectations of the organization.
Some of the problems in addressing expectations arise from simple miscommunications and misunderstanding. Still some from because planners do not take the time to understand and discuss expectations with the organization. It is important to discuss with the organizations, defining terms carefully and precisely to avoid simple misunderstandings. The communication channels with the planner remain open so that expectations can continuously be defined and specifications made clear.
A common error among planners is the simple lack of documentation. Sometimes, the planner has not misunderstood the expectations but because they did not document the same, they maybe unsure of what is expected. When people agree to sit down, agree and document what they have discussed, they give authority to the written documents. In any business and project, written documents should automatically be used in place of memory, (Dawson and Dawson 1998). Even those who claim to have the best memories can often forget small details at the most inopportune moments.
When planners fail to carefully manage the expectations of the organization, there is likely to arise major conflicts in the implementation of the plan. The organization could demand changes to a tirelessly and diligently prepared plan. On the other hand the planner may feel that the demands of the organization and changes requested are not realistic. All in all, there is a general dissatisfaction because the plan did not address the expectations of the organization. Zwikael and Globerson (2004), state that in other cases, the planner may focus s o much on addressing the expectations of the organization which may be unrealistic. Because they are striving to make unrealistic goals realistic, chances are that they will be frustrated and in the end develop a plan that has less about quality and integrity. Where the organization goals are deemed to be unrealistic, it is much wiser for the planner to politely and with the use of facts highlight how such expectations cannot be met. In the end, the expectations agreed upon should be not just realistic but also achievable through the plan to be set forth.
It is important for the planner to note that the expectations he addresses in the plan will be the responsibility of the project team and manager. If such expectations were below par, the project team may become frustrated, expecting larger results but only being able to make small milestones. On the other hand if they were unrealistic and not achievable, the team is likely to lose motivation as the purse goals that are unrealistic, (Richman 2002). In the end the frustration and exhaustion of the project managers and teams will translate to complete failure of the project. It is not surprising to find stalled projects and unsuccessful ventures which stand out to organizations and communities as sore thumbs and which began with the simple poor addressing of expectations by the planner. Most in fact become stalled at the first stages when the stakeholders realize that expectations are far from achievable.
PREPARING THE BUDGET AND WORK PLAN
Often planners work under tight schedules, with managers and their teams determined to begin working almost immediately. With this in mind, it is common for planners to avoid the hustle of estimating costs and time. This is the most costly mistake for planners as it reflects on the process of project control. Stakeholders expect accurate costs and time estimations. Poor cost and time estimations are likely to lead t false expectations and uncertainty. In order to provide enlightened estimates, planners can be guided by the following aspects:
Responsibility: when planning for costs and time, it is best for planners to work with people who understand the specific tasks. These individuals are enlightened on the situation at the ground in addition to possessing internal knowledge on how such things work. Of course such individuals should be independent of the organization and the project to avoid biasness in the cost tracking. Once the planner has arrived on particular costs they can liaise with the stakeholders to ensure that they agree and accept responsibility for the budget and work plan, (Leus and Herroelen 2004).
Use several different sources of information: a common error with planners is to collect information such as the costs from one source rather than several sources which could be more beneficial. Several sources provide varying ranges of time and costs, the average of which reflects best the situation on the ground. One source of information may prove to be less than reliable.
Use independent tasks: when preparing the work plan and budget, planners are often tempted to inter-relate all the activities. This leads to unrealistic plans and estimates. Each task should be treated independently to ensure that it receives the right attention in terms of resources, cost and time to ensure success. Only when each individual task has been tackled independently should the planner combine and rationalize what is now the cost and time for the tasks.
Add risk assessment to the plan: planners need to understand that some tasks carry a much greater risk in terms of cost, resources and even time. Such risk assessment should be included in the budget and contingencies made for the same. Adding the risk assessment allows the stakeholders to be aware of and plan for the contingencies. Without this, there is risk of going beyond the budget or even experiencing delays as solutions are sought when the risk comes into play.
REFERENCES
Bond, W. T. F. (1996). Design project planning: A practical guide for beginners. London: Prentice Hall.
Burke, R. (1999). Project management: Planning and control techniques. Chichester, England: J. Wiley.
Burton, C., & Michael, N. (1994). A practical guide to project planning. London: Kogan Page.
Carmichael, D. G. (2006). Project planning, and control. London: Taylor & Francis
Devaux, S. A. (1999). Total project control: A manager’s guide to integrated project planning, measuring, and tracking. New York: Wiley.
Dawson, R. J., & Dawson, C. W. (1998). Practical proposals for managing uncertainty and risk in project planning. International Journal of Project Management, 16(5), 299-310.
Gaynor, A. K., & Evanson, J. L. (1992). Project planning: A guide for practitioners. Boston: Allyn and Bacon.
Haugan, G. T. (2002). Project planning and scheduling. Vienna, Va: Management Concepts.
Klein, H. (2008). Basics project planning. Basel: Birkhäuser
Lester, A. (2003). Project planning and control. Oxford: Elsevier Butterworth-Heinemann.
Leus, R., & Herroelen, W. (2004). Stability and resource allocation in project planning. IIE transactions, 36(7), 667-682
Lewis, J. P. (1995). Project planning, scheduling & control: A hands-on guide to bringing projects in on time and on budget. Chicago, Ill: Irwin.
Melton, T. (2008). Real project planning: Developing a project delivery strategy. Amsterdam: Butterworth-Heinemann
Platje, A., Seidel, H., and Wadman, S. (1994). Project and portfolio planning cycle: project- based management for the multi-project challenge. International Journal of Project Management, 12(2), 100-106.
Potts, D. (2002). Project planning and analysis for development. Boulder, CO: Lynne Rienner Pub.
Rad, P. F., & Anantatmula, V. S. (2005). Project planning techniques. Vienna, Va: Management Concepts.
Raz, T., and Shenhar, A. J. (2003). An empirical analysis of the relationship between project planning and project success. International Journal of Project Management, 21(2), 89- 95.
Richman, L. L. (2002). Project management step-by-step. New York: Amacom
Tomczyk, C. A. (2005). Project manager’s spotlight on planning. San Francisco, Calif: Harbour Light.
Vargas, R. V. (2008). Practical guide to project planning. Boca Raton: Auerbach Publications.
Zwikael, O., & Globerson, S. (2004). Evaluating the quality of project planning: a model and field results. International Journal of Production Research, 42(8), 1545-1556.
With a student-centered approach, I create engaging and informative blog posts that tackle relevant topics for students. My content aims to equip students with the knowledge and tools they need to succeed academically and beyond.
by Herman Bailey | Jan 24, 2026 | Essays |
The Fearon decision in R V. Stephenson
The Fearon case was discussed and mentioned in paragraph 67 of the decision-making process. This paragraph concluded that the first search into the accused’s phone was within the legal limits set for investigative officers. However, with the in-depth analysis and search into the activities of the accused phone, the judge agreed that the detectives may have crossed some boundaries and violated the rights of the accused. However, the evidence collected from the accused’s phone was admitted and thus weighed heavily on the court’s decision.
The first search
During the arrest, the accused did not object to officers checking his phone the first time. Instead, while he was being searched in plain view of his phone, he watched the officers go through the phone. A different matter would have arisen had the accused been vocal in challenging the search for his phone. Since the accused insisted that his rights were violated, he needed to have voiced his concerns in court and at the time of the search. The judge’s decision would have been in his favor by invoking his right to privacy and requesting a warrant for the officers to access his phone.
On the other hand, the events superseding the search for his phone did not help to rule in his favor. The judge felt that the search was essentially in plain sight and without objection; therefore, it was simply a matter of concession. The accused essentially agreed to the search, negating the need for a warrant.
The second search
Officers conducted the second search after the arrest to find evidence to solve the case and use against the accused. In this case, the judge found that while this search would have been against the rights of the accused, it was in the interest of justice and truth. To determine this, the judge had to examine the extent of the evidence gathered from his decision. He found the evidence lacked relevance and could not harm the accused in his pursuit of justice.
Should the evidence have been excluded, it might have been possible for the accused to argue the facts presented in the court. The accused insisted that all he did was drive around with two strangers while simultaneously indicating that he used his phone far from the crime scene. However, the admission of the phone evidence raised doubt about his activities, thereby creating a loophole that the prosecutor used to get his verdict.
Considering the Charter of Rights and Freedoms
The judge’s decision is based on the analysis of the trial judge. Under making the decision, the trial judge in the Fearon case showed that the three aspects of section 24, as determined and established in R V. Grant, were fully satisfied.
- The seriousness of the Charter-infringing state conduct: the accused argued that simply because he had his phone at the time of arrest, the arresting officer should have waited for a search warrant. However, the trial judge considered that the phone did not have a password. The lack of a password reduced the seriousness of the infringement. This is because had the phone fallen or become lost, anyone could have had access to the information therein.
- The impact of the breach on the Charter-protected interests of the accused: This is whereby the evidence from the phone alone would have been enough to convict the accused. The only evidence gathered was pictures of a gun and other incriminating pictures. However, the prosecution still had the burden of proving that these pictures were relevant to the case instead of just entertainment in r private collections. Therefore the impact of the evidence would be low since the evidence alone could not convict the accused. The evidence could be used to support and strengthen the prosecution’s claims.
- Society’s interests in the adjudication of the case on its merits: the accused was involved in a crime of violent nature. The possession of a gun would have caused severe harm to society’s citizens. The trial judge highlighted that armed robbery in itself is a crime that could lead to the loss of valuable property within the jeweler’s periphery and the loss of lives. Whenever the consideration of life is concerned, society’s interests increase, and such interests take precedence over the accused’s privacy, as was established in this case. The phone’s evidence must be admitted for the good of society and the future of all people within.
Does the Manley decision bind the Court of Appeals for Ontario?
In the court of Appeals case of Manley, the judge indicated that all accused, that is, anyone under arrest, can expect a search into their phone. This immediate search is protected under the law because officers often gather important evidence that could help further the case’s investigation and gathering of evidence. At the time of arrest, the phone is considered part of the evidence collected and warrants a proper search. However, any further search into the phone may require a warrant. It should be noted that in this case, the accused had no password at the time of the arrest. If the phone has a password, the accused or arrested person is not required to provide the same. He can opt not to give or assist the officers in their investigation, and such lack of assistance will not be held against him during the period the case is presented to the court. However, a lack of a password is like the lack of objection in the case of Stephenson; it generally means that the individual has conceded to the search and, therefore, privacy rights have been violated. The evidence gathered can therefore be used by the prosecution to prove its case. Cell phones are held in different accounts with the accused’s laptops, computers, and homes. Searches into these are considered a violation of privacy, thereby requiring warrants.
Fearon C.A. decision
The court of appeal 2011 upheld the CA decision. The delicate line between an accused’s privacy and the search for justice is often called to question in these cases. The main bone of contention is often the interest of society versus that of the accused. Is the accused looking to protect his privacy or simply refusing to submit evidence that can be used to provide justice to society? While the accused has a right to privacy, such a right cannot be upheld without considering the justice and truth that society expects.
Summary Of R V. Fearon
The case begins with the arrest of the accused, Fearon, in the lobby of his building. This was after a jewelry store robbery in which one of the witnesses recalled a license plate that led officers to his building. During the subsequent search of the accused, a cell phone was found. The officer did not believe the phone would yield any reasonable evidence but proceeded to search and look into it. At the time of the search, Fearon was still under arrest and could see his phone being searched by the officer. He did not raise any objections. During the search, the officers uncovered a text message confessing to the crime and incrementing photos. Further unwarranted search into the hone yielded no other evidence.
The accused’s argument was based on violating his privacy, while the prosecution felt that no rights were violated in the search. The judge had to determine the authenticity of the evidence and whether such evidence should be presented and used in the decision. It is important to note that the officers lacked sufficient evidence to hold the accused. The text message, on the other hand, was an immediate confession to the crime, thereby rendering strength to their case. The Judge felt that the evidence would be submitted in the interest of justice because the accused did not object. With this evidence in place, the accused was found guilty of armed robbery.
With a student-centered approach, I create engaging and informative blog posts that tackle relevant topics for students. My content aims to equip students with the knowledge and tools they need to succeed academically and beyond.
by Herman Bailey | Jan 24, 2026 | Essays |
Introduction
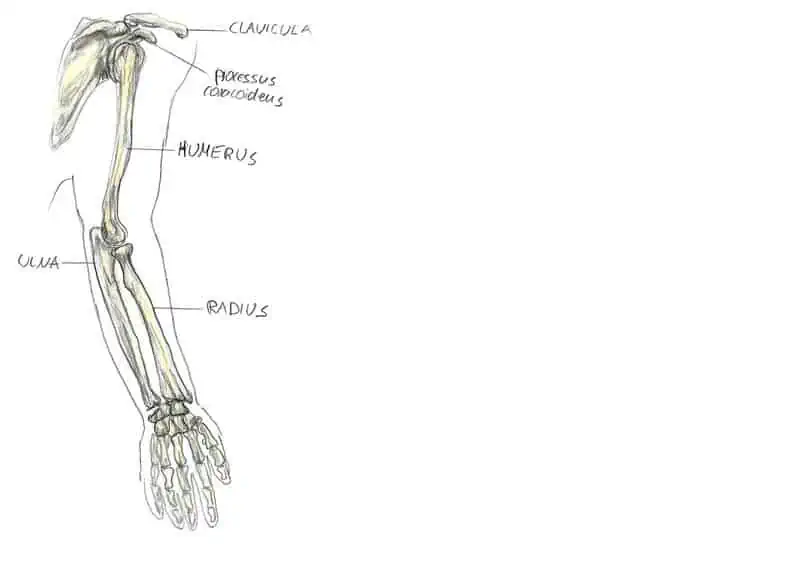
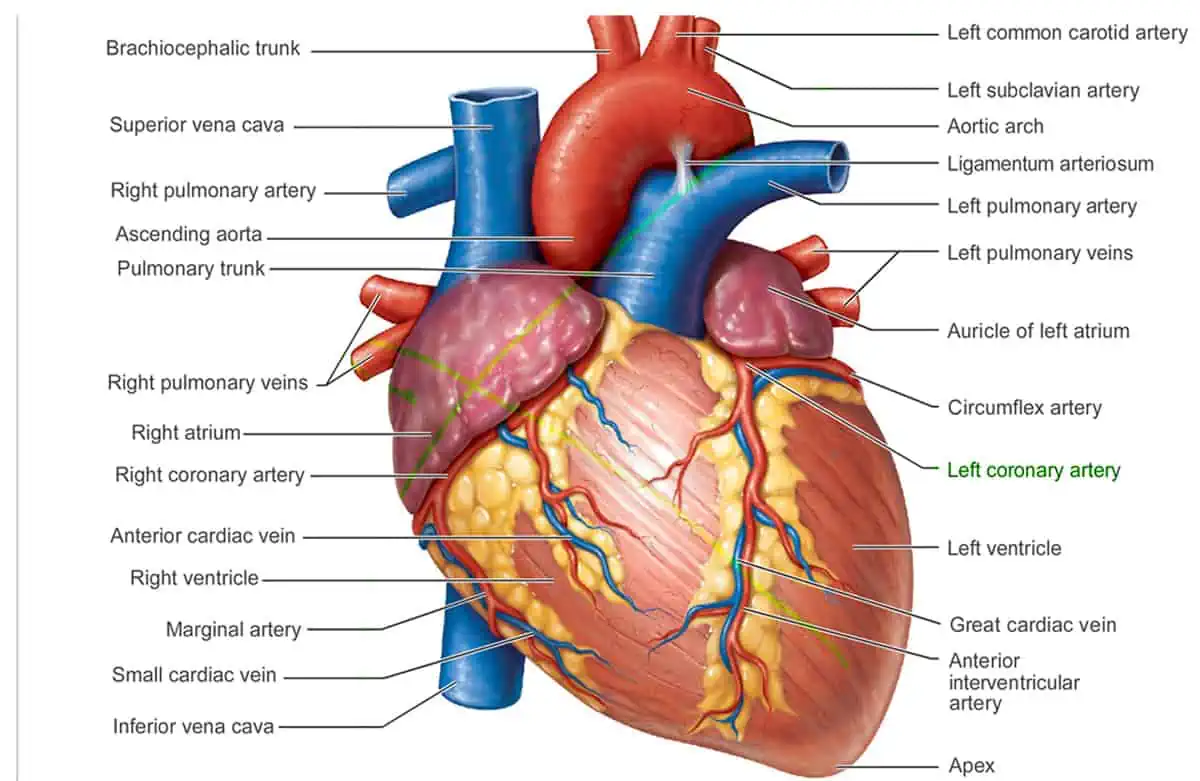
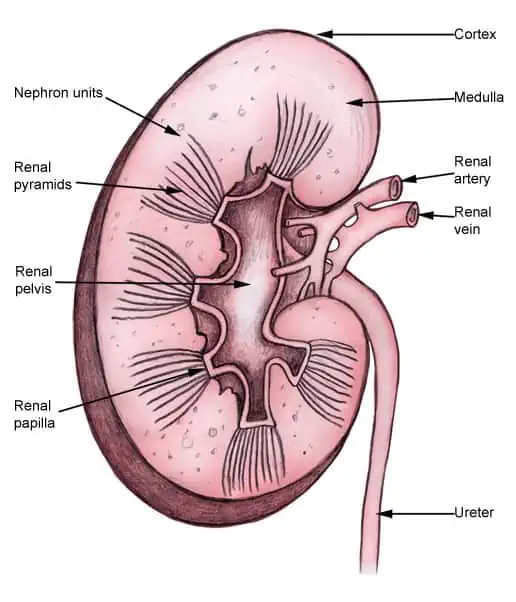
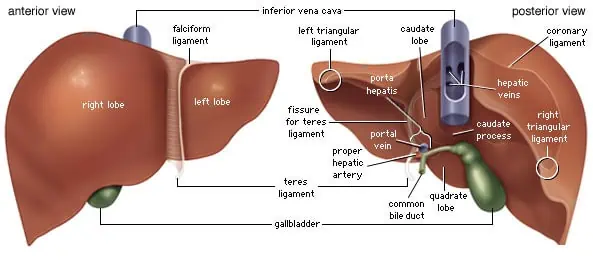
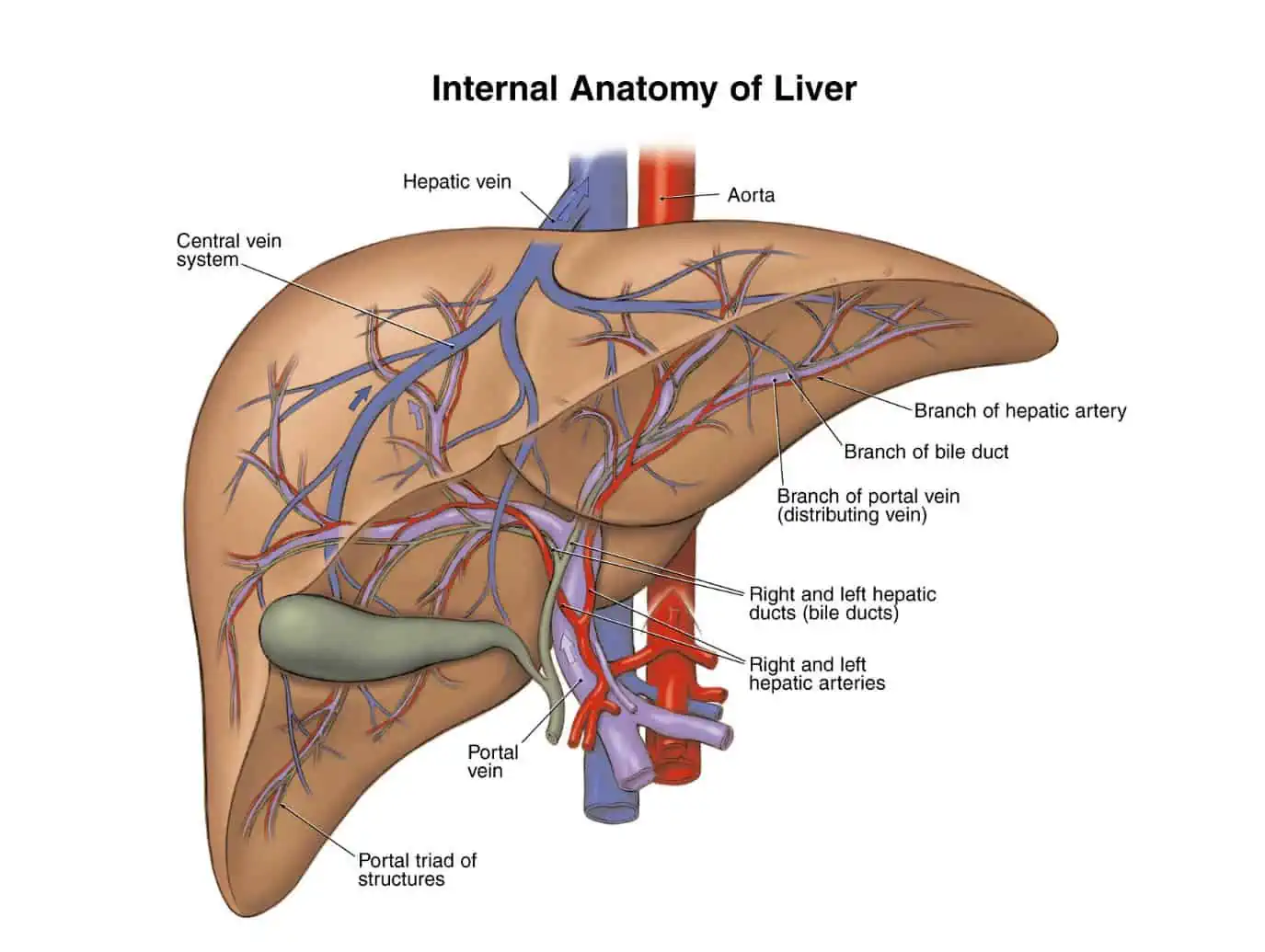
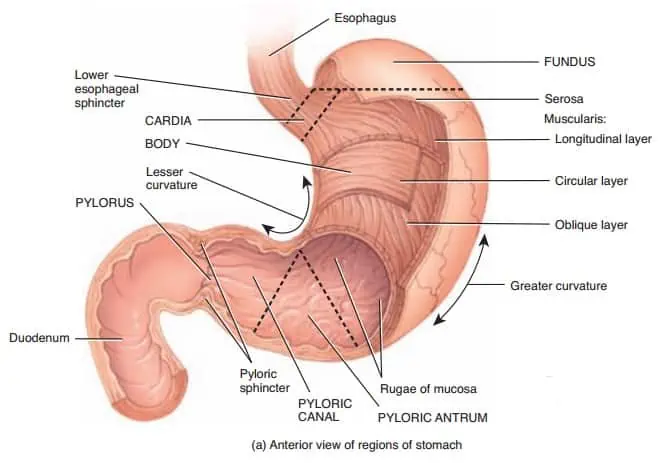
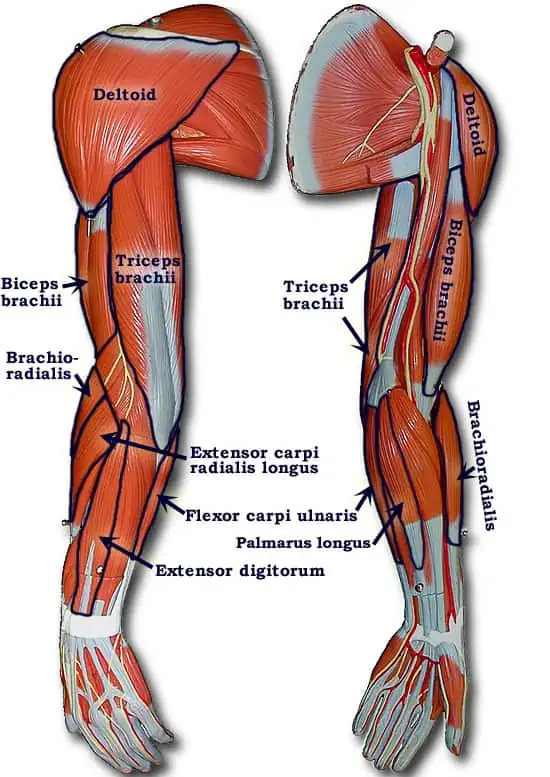
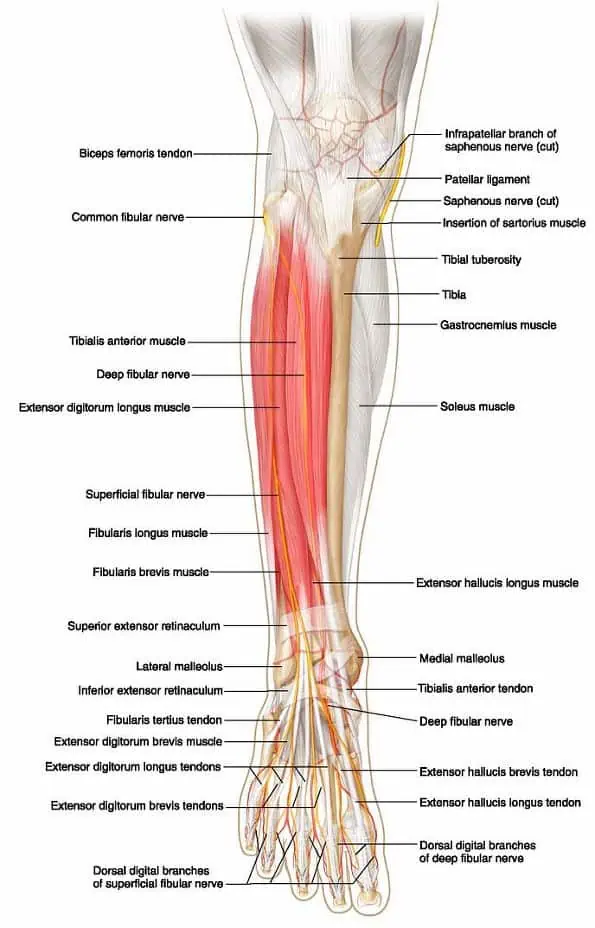
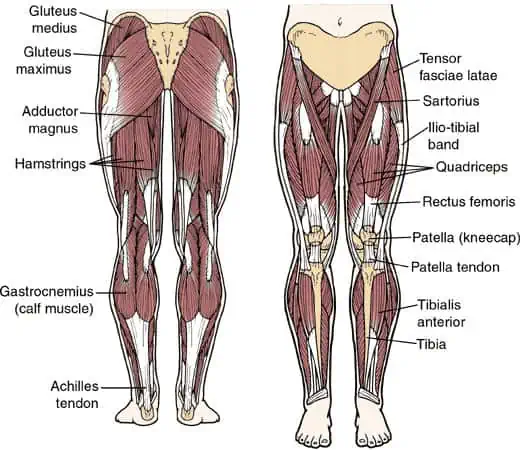
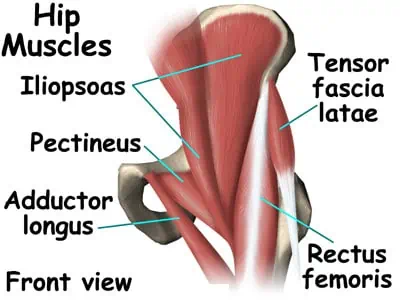
This paper discuses ten individual case studies of different anatomical regions of the human body. Each individual case study has been briefly justified by providing the reasons why the case were chosen for the study and also provide a clinical context for the case. In addition, each case study has provided an overview and review of the imaging protocol that were performed in each image to demonstrate why the imaging protocol was performed and also to answer some of the relevant clinical questions poised for each case study. This included elaboration on the anatomical planes, structure and whether contrast media has been used or is needed to clearly show anatomical structures of each anatomical image. All the images used in this paper are anonymised to avoid breaching patient confidentiality. Finally, each case study has been provided with detailed annotation for each images. The case studies used included three for skeletal parts, four for human body organs, and three for muscular skeletal muscles anatomical regions
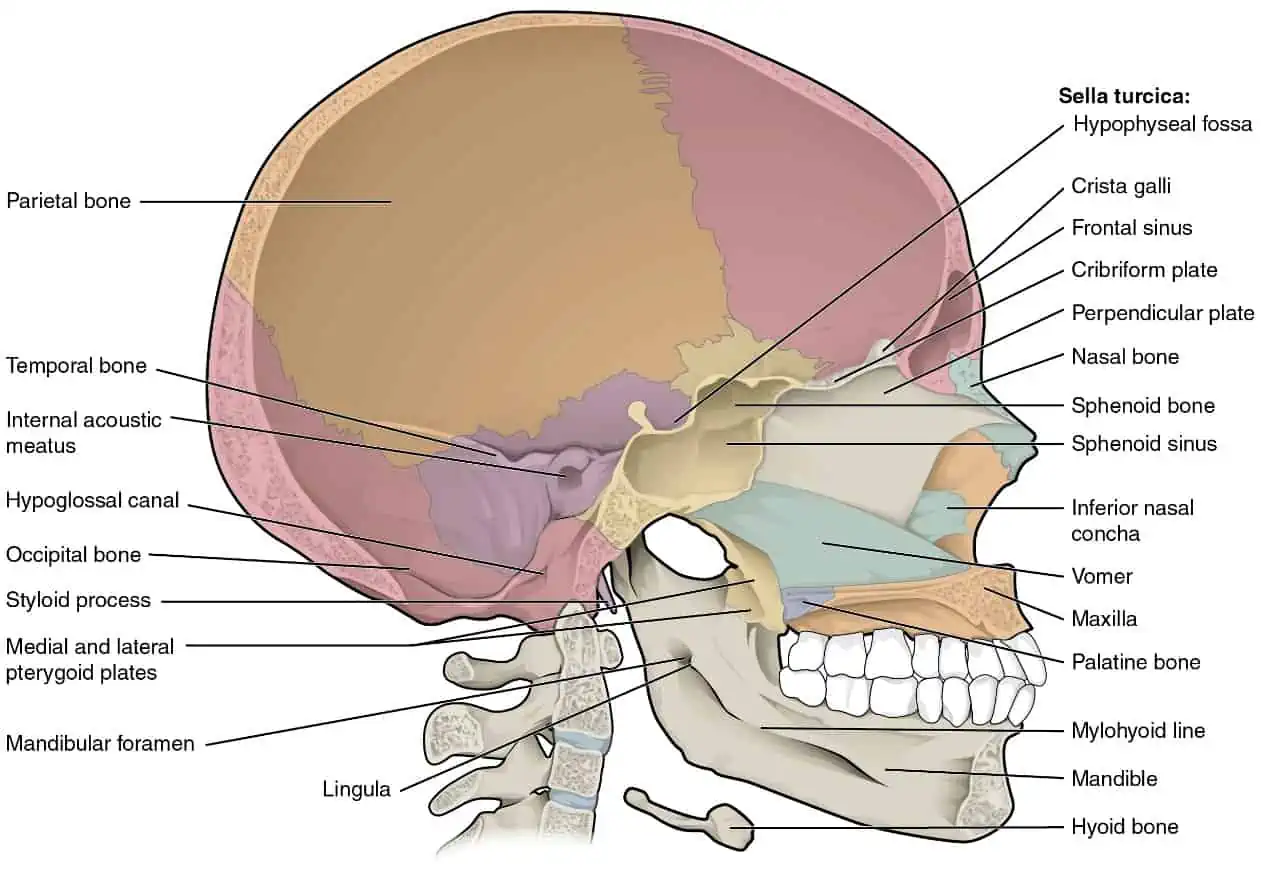
1.0 Case study 1: Skull
1.1 A brief justification
The bones found on the head play a critical role protecting the brain, nerves, sensory organs and the blood vessels of the head from mechanical damage. These bone’s movements by the muscles attached to the head provide for speech, eating, facial expressions and movement of the head (Larsen, 1997). According to Mays (1999), the skull is made up of 22 facial and cranial bones tightly fused together except the mandibles. The case was chosen because the skull is very vital to humans since it encases and protects the human brain and other special sensory organs of hearing, vision, taste, balance and smell
The skull also has muscle attachment points of the neck and the head located on the skull’s exterior surfaces and allow for movements such as facial expression, speech and chewing. Teeth are also deeply rooted in the sockets of the maxillary and mandible bones. Moreover, the upper sections of the respiratory and digestive tracts are also housed within the hollow nasal and oral skull cavities.
1.2 Overview & review of the imaging protocol performed
The skull images of this case studies has been presented in different anatomical planes, that is transverse, sagittal and frontal planes. Moreover, different anatomical directions has been applied in the imaging of the case study skull such as the frontal, lateral, posterior and superior anatomical directions. The anatomical structures of the skull has been labelled in the diagram for easier comprehension. A contrast media particularly a colored imaging is also helpful especially in the superior view of the cranium to differentiate the lobes, fissures, canals, openings and the sutures
1.3 Detailed annotation of all normal anatomy demonstrated on each image
1.3.1 Anterior view of the skull
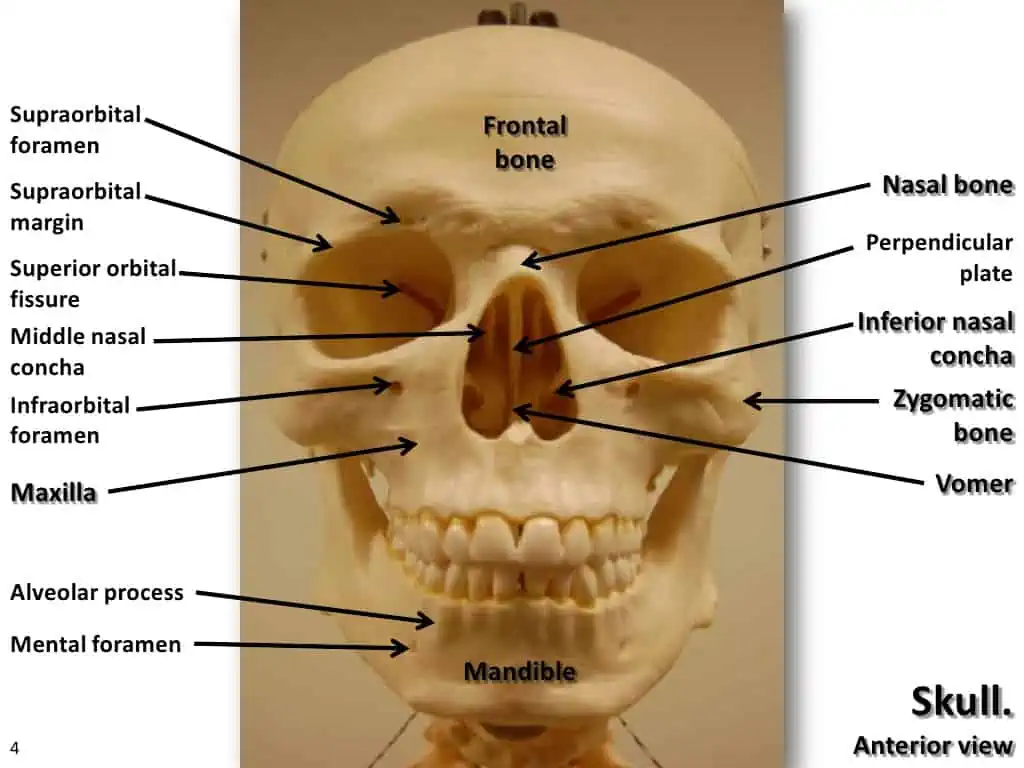
The skull’s anterior view consisted of the facial bones in addition to supporting the structures and eyes of the face. The anterior view of the skull is majorly dominated by the orbits openings and nasal cavity. Also present are the lower and upper jaws and their respective teeth as shown in Figure 1. The orbit in the anterior part of the skull is the socket housing the eyeball and the neighbouring muscles that assist in the movement of the eyeball or opening the upper eyelid. Supraorbital margin is the anterior orbit’s upper margin. Supraorbital foramen is a small opening located near the supraorbital margin mid-point. Supraorbital foramen provides a passage for the skulls sensory nerve to the forehead skin. Infraorbital foramen is located below the orbit and is the emergence point for the sensory nerve supplying the anterior face just below the orbit (OpenStax, n.d).
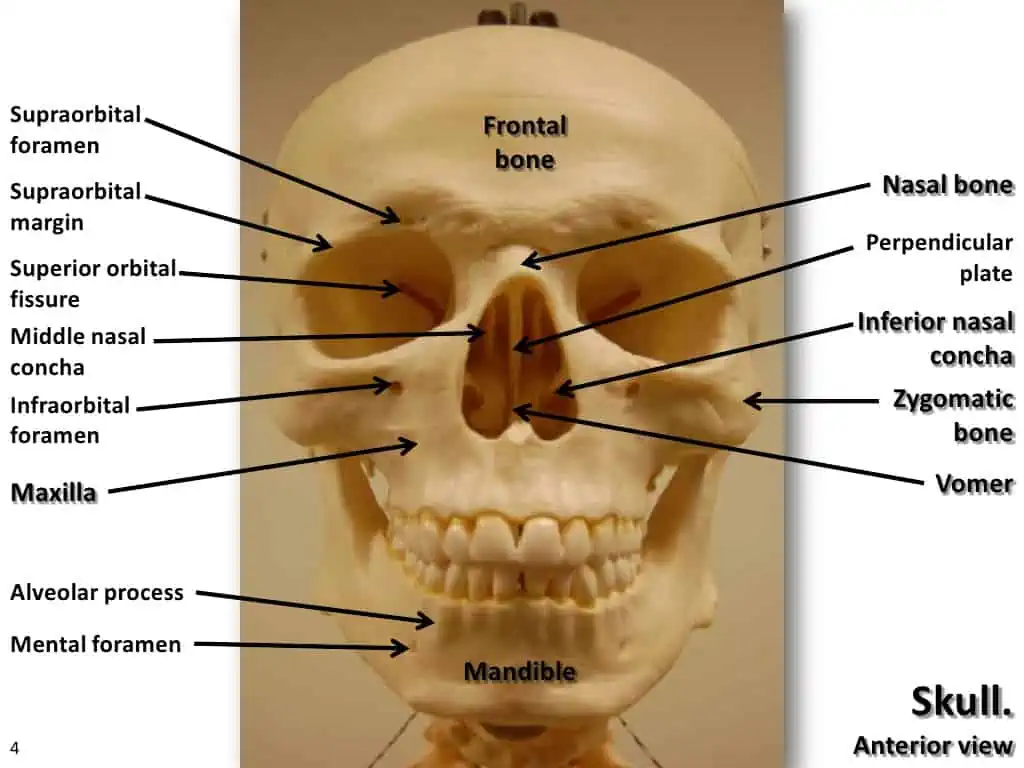
Figure 1: Frontal view of the skull
Inside the skull’s nasal area, the nasal septum divides the nasal cavity into halves. The perpendicular plate of the ethmoid bone forms the nasal septum’s upper portion and Vomer bone forms the lower portion. Every side of the nasal cavity has shape of a triangle, with a broad inferior space narrowing superiorly. Closely looking into the nasal cavity from the skull’s front, there are two projecting bones from each lateral wall. Inferior nasal concha is the larger among these projecting bones and it is an independent skull bone (Roberts & Manchester, 2010). Middle nasal concha is located above the inferior nasal concha, and it forms part of the ethmoid bone. Lastly, superior nasal concha which is the third bony plate and also part of the ethmoid bone is out of sight and smaller and is located above the middle concha. The location of the superior nasal concha is in the upper nasal cavity and lateral to the perpendicular plate as shown in Figure 1 (OpenStax, n.d).
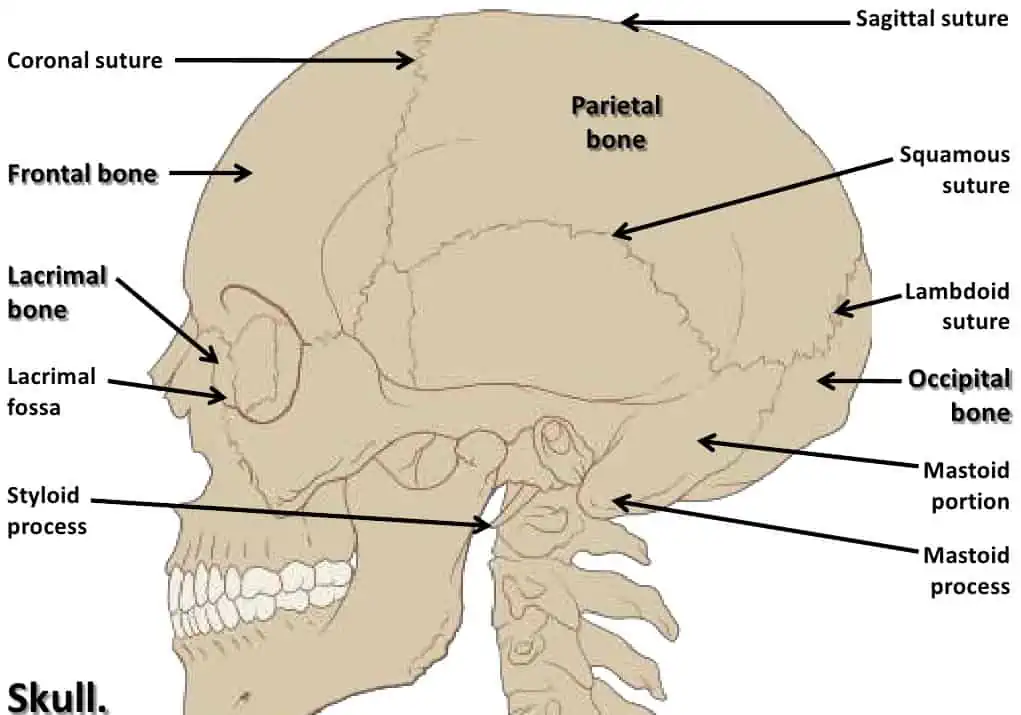
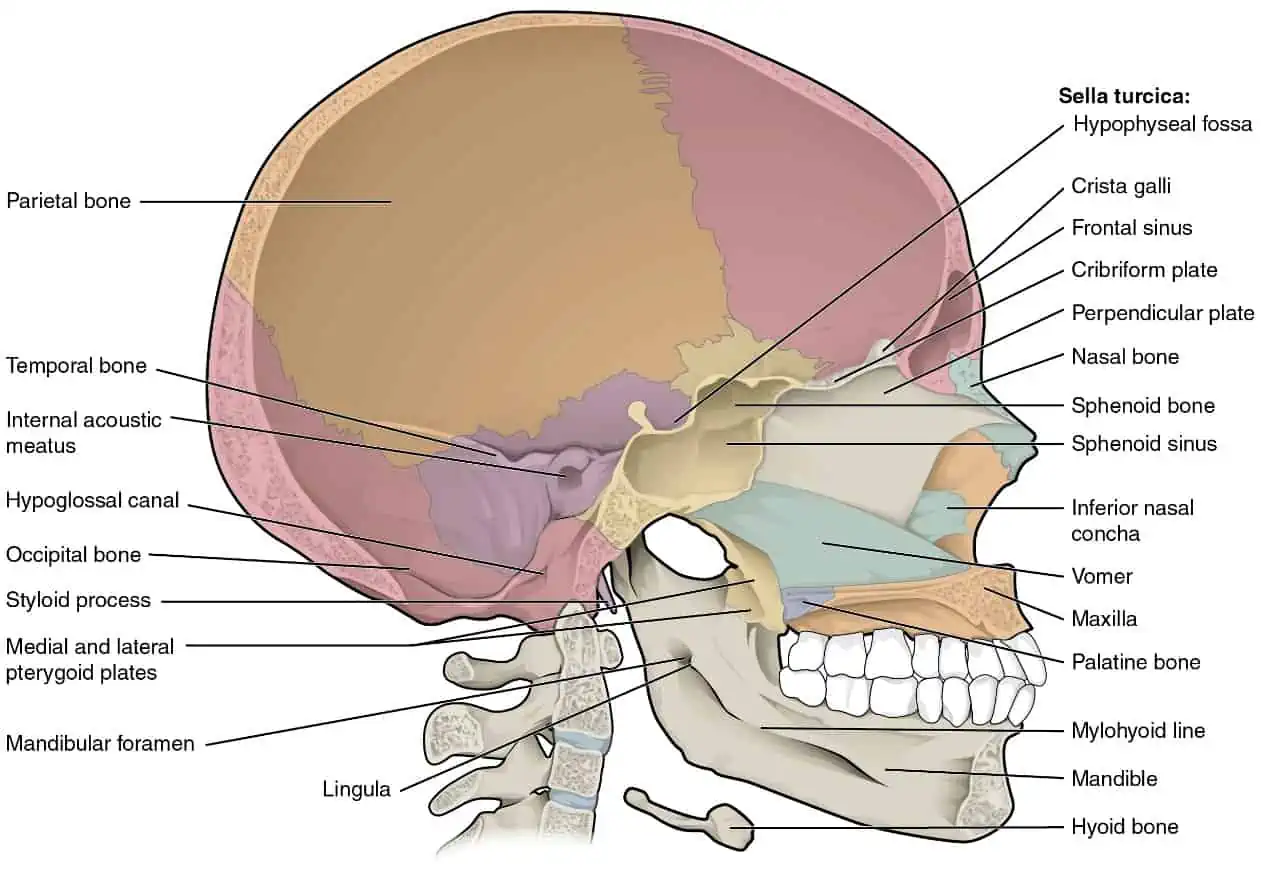
1.3.2 Lateral view of the skull
The lateral view of the skull is dominated by the rounded, large brain case above and the lower and upper jaws with their teeth as shown in Figure 2 and 3. Zygomatic arch is a bridge of bone that separates these areas. OpenStax (n.d) defined zygomatic arch as the bony arch located on the side of the skull spanning from the areas just above the cheek to the area above the ear canal. Zygomatic arch is formed by two bony processes junction: zygomatic bone temporal processes (cheek bone) which is a short anterior component and the zygomatic process of the temporal bone which is longer posterior portion that extends from the temporal bone forward (OpenStax, n.d). Therefore, the zygomatic process (posteriorly) and the temporal process (anteriorly) join together to form the zygomatic arch. OpenStax (n.d) pointed out that one of the major muscles pulling the mandible during chewing and biting upwards originates from the zygomatic arch.

Figure 2: Lateral view of the skull.
According to White & Folkens (2005), on the brain case ‘lateral side, there is a shallow space above the zygomatic arch level called the temporal fossa. Additionally, deep to the mandibles deep portion and belwo the zygomatic arch level is another space referred to as the infratemporal fossa. Larsen (1997) stated that both infratemporal fossa and temporal fossa contain muscles acting on the mandible during the process of chewing.
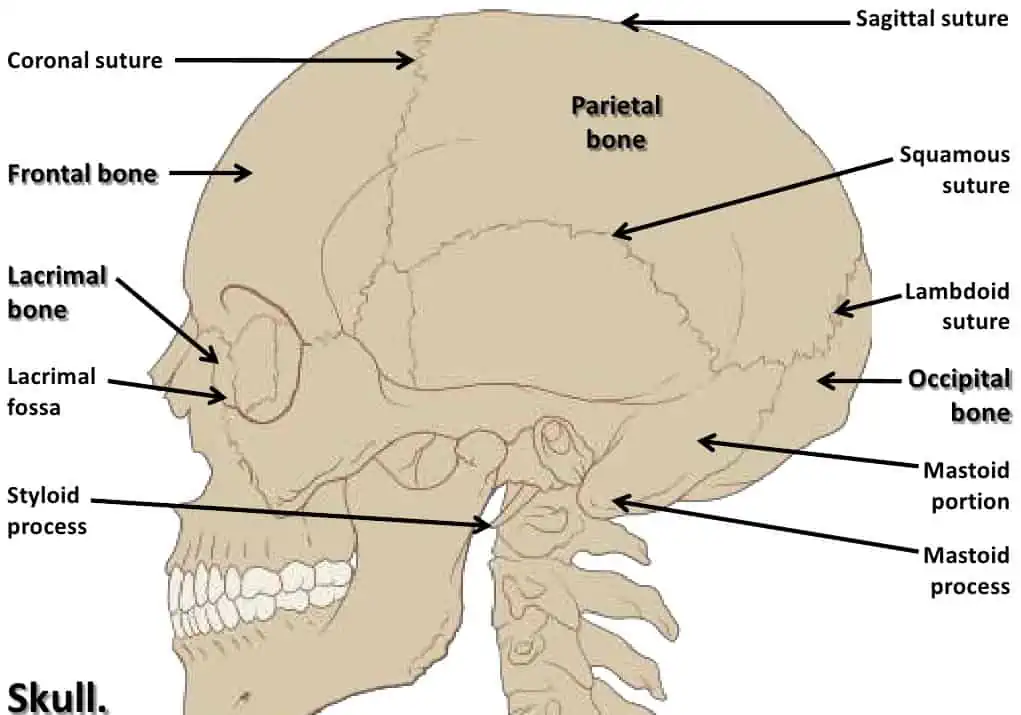
Figure 3
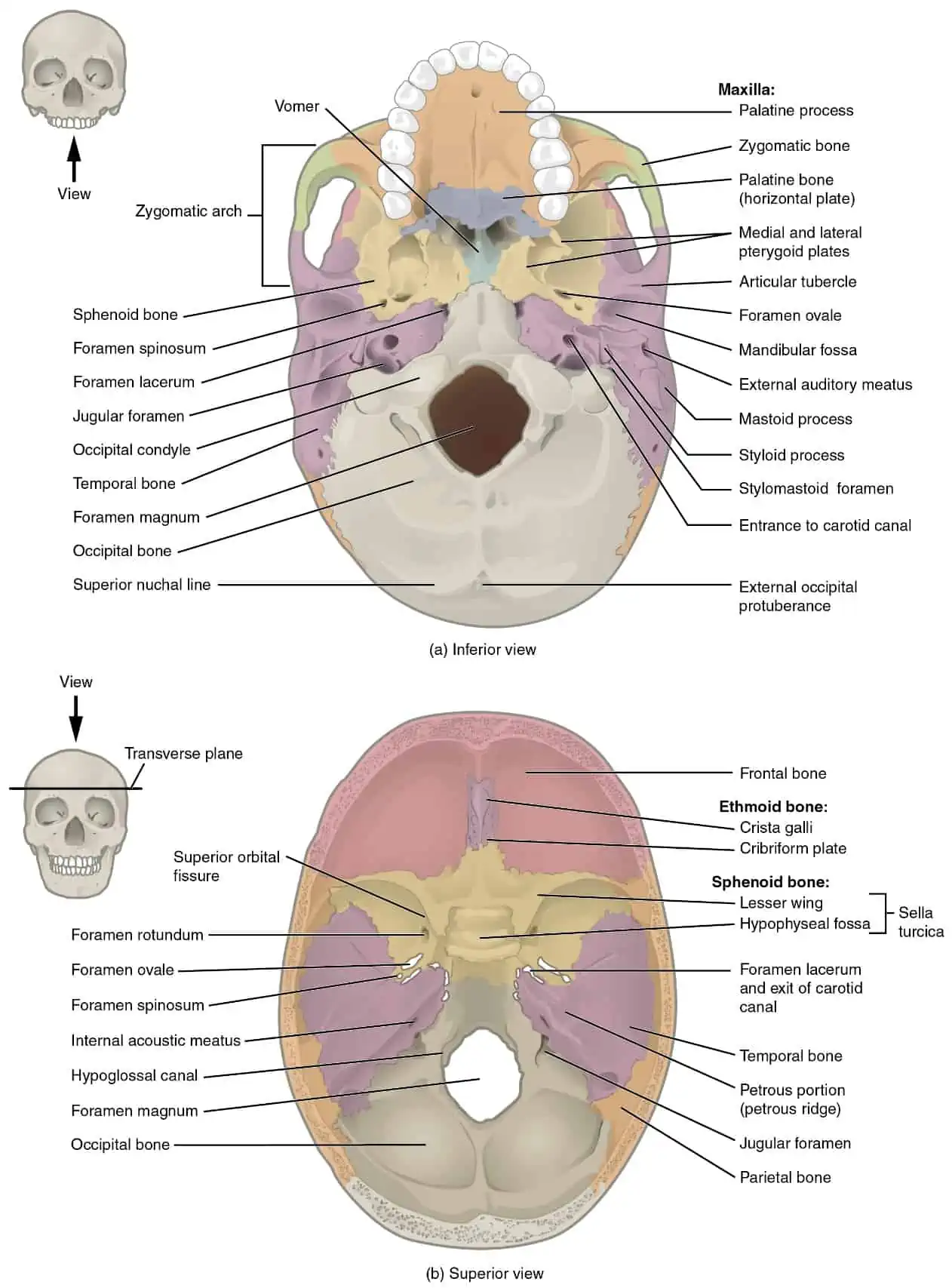
1.3.3 Internal and external views of the skull base
Part (a) of Figure 4 shows the hard plate that is anteriorly formed by the maxilla bones ‘palatine processes and posteriorly by the palatine bones ‘horizontal plate. Part (b) of Figure 4 shows the complex cranial cavity floor that is formed by ethmoid, frontal, temporal, sphenoid and occipital bones. The sphenoid bones’ lesser wings separates the middle and anterior cranial fossae. In addition, the petrous ridge (temporal bones petrous portion) separates the posterior n and middle cranial fossae.
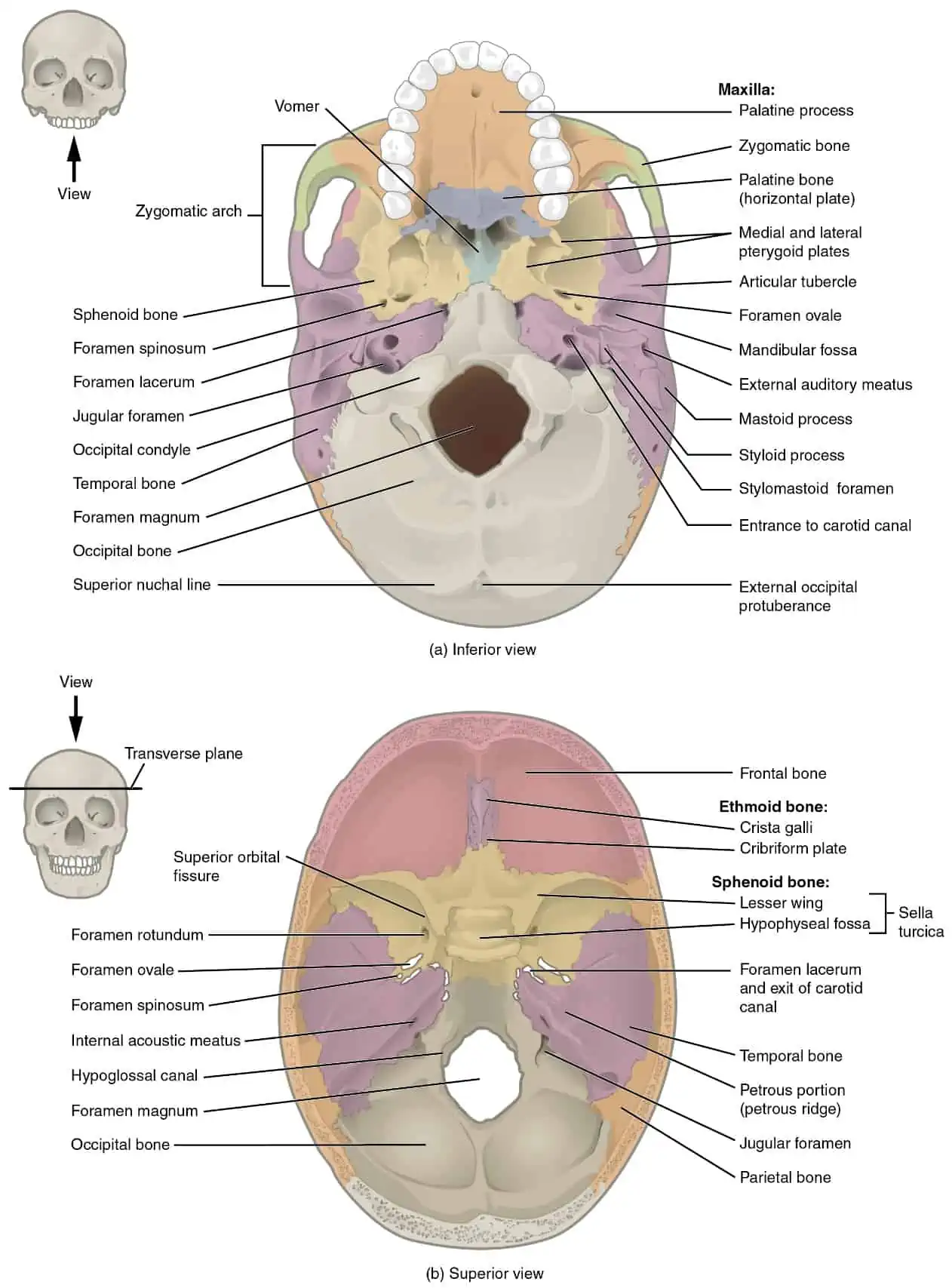
Figure 4: Internal and external parts of the skull
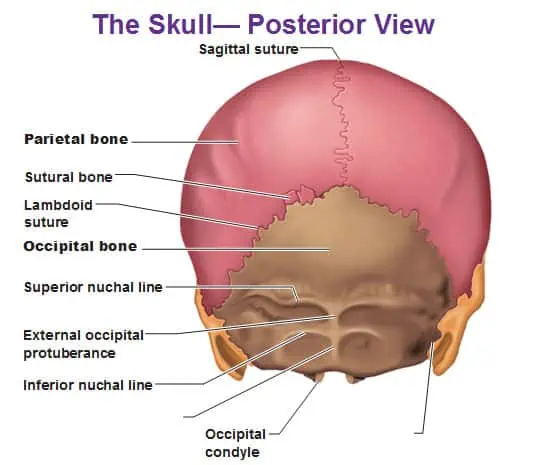
1.3.4 Sutures of the skull
According to Mays (1999), suture is a joint between skull adjacent bones that are immobile. The narrow gap that exists between the bones is filled with fibrous connective dense tissue that unites the bones. Roberts & Manchester (2010) pointed out that the long sutures found on the brain case bones are not straight rather follow tightly twisting irregular paths. The twisting lines serve the purpose of tightly interlocking the adjacent bones hence providing additional strength to the skull for protection of the brain
Sagittal and coronal sutures are found on top of the skull. The coronal suture runs across the skull side to side, within the coronal plane as shown in Figure 3. Moreover, it joins the left and right parental bones to the frontal ones. The sagittal suture, on the other hand, posteriorly extends from the coronal suture and runs along the midline at the skull’s top in the sagittal plane as shown in Figure 3, 6 and 7. Sagittal sutures unites the lefts and the right parietal bones (White & Folkens, 2005).

Figure 5
Figure 6
On the skull’s, the sagittal suture ends by joining the lambdoid suture which extends laterally and downwards to either sideway from where it meets with the sagittal suture. The lambdoid suture runs and joins the occipital bone to the left and right and temporal bones as shown in Figure 3 and 5.
The squamous suture is found on the lateral skull and it unites the parietal bone with the temporal bone’s squamous portion as shown in Figure 3.pterion is located at the four bones intersection and is a small suture line region that is capital H shaped uniting the parietal, frontal, temporal bone’s squamous portion, and sphenoid bone’s greater wing. Pterion is the skull’s weakest part (Larsen, 1997).
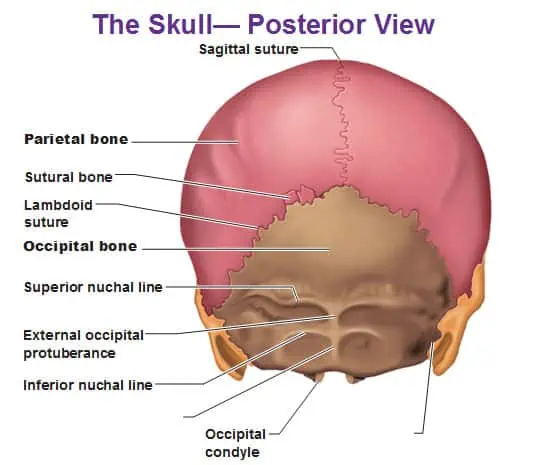
Figure 7
Sagittal section of the skull
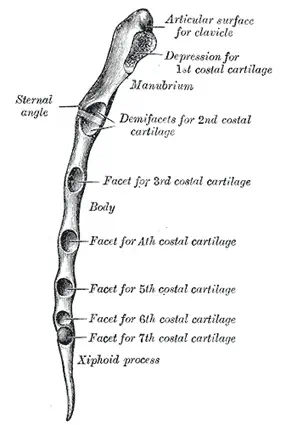
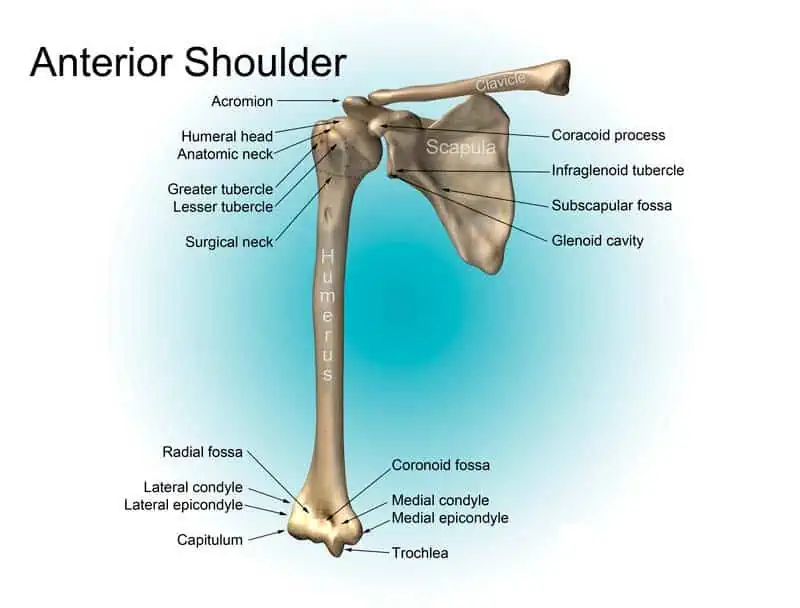
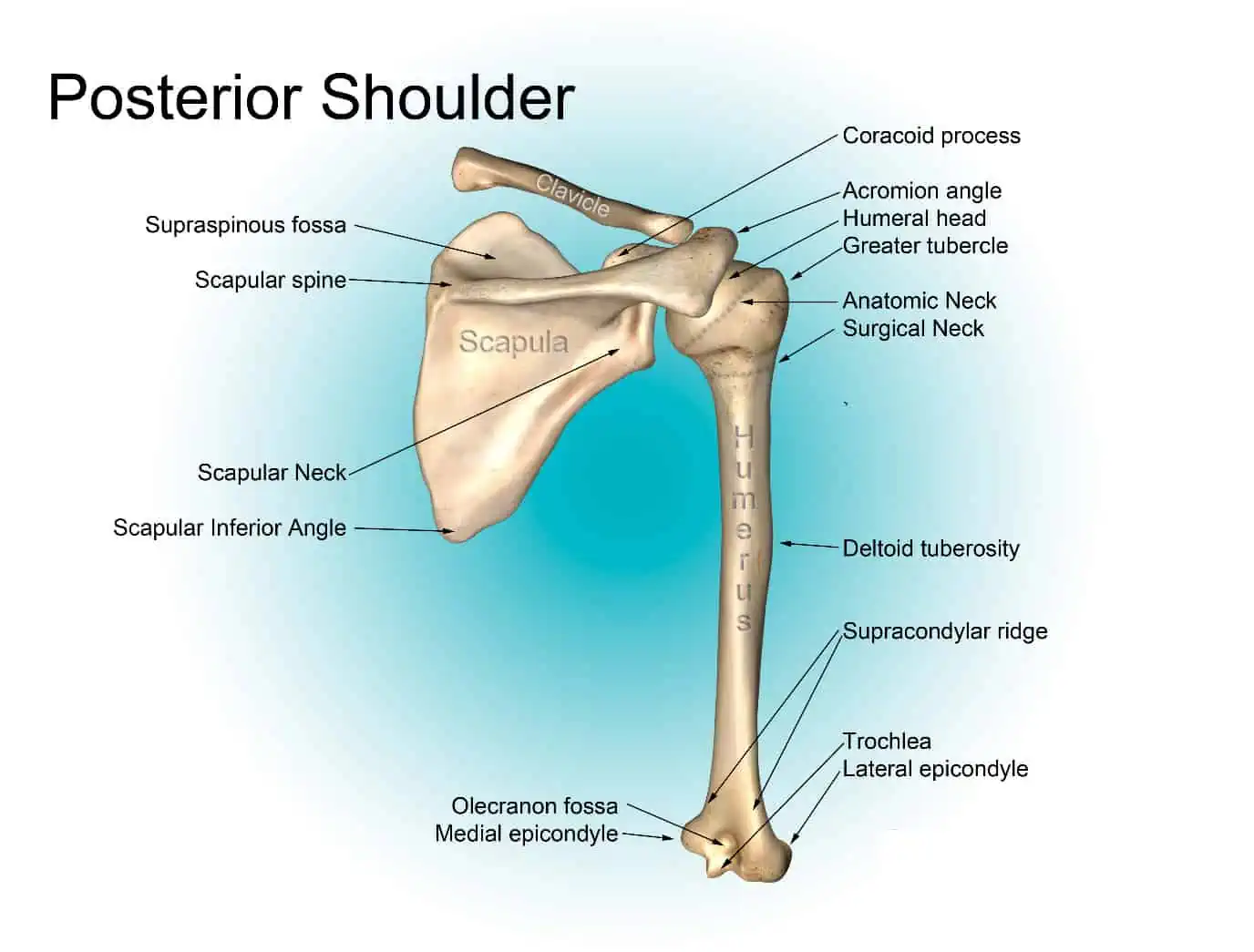
2.0 Case study 2: Thoracic cage
2.1 A brief justification
The thoracic cage consist of ribs paired in 12 sets or curved bones surrounding the chest region. The thoracic cage helps in protecting the blood vessels and the vital organs in addition to expanding and contracting alongside the lungs for efficient breathing. Thoracic cage was chosen as case study in this paper because of its significant role in protecting the vital body organs such as the heart and lungs. The rib cage also helps assists during breathing using the intercostal muscles which lifts and lower the rib cage. The first seven ribs in the thoracic cage are referred to as the true ribs (Flynn, 1996).the ribs are directly connected to the sternum via costal cartilage which adds elasticity to the whole thoracic cage allows the ribs to move. The other five remaining ribs are referred to as the false ribs (Hale et al, 1983). Three ribs out of the false ribs are connected to the sternum via cartilage while the remaining two are not connected to the sternum but only the vertebrae hence referred to as the floating ribs as shown in Figure 8 (Kenyon, 1989).

Figure 8
Generally, ribs of the human being beings increase in length from rib one to rib seven and start decreasing n length again up to rib 12. Because of the change in size, the human ribs progressively become slanted (oblique) from rib one to rib nine, then again less slanted to rib 12.
2.2 Overview & review of the imaging protocol performed
The imaging protocol used in this study varied to give a clear view of different anatomical labels and directions of the thoracic cage. First, some x-ray was used as an imaging protocol to show the rib cage bones and the upper part of the spinal cord. Additionally, the images has been taken from different views which included rib projection on expiration, on inspiration and during fast and slow breathing. The views of the images in this case study were also taken at 300 and 450 angles sequentially in anterior oblique positions. The images of this case study also indicate that the subjects were standing in erect positions. Other imaging techniques used include line sketch images, CT scan, Ultra sound and bone scan.
The images are presented in different anatomical planes such as sagittal, frontal and transverse planes. The anatomical regions of the images are labelled clearly in each image for distinction. Contrast media were also used in some images to help in distinguishing key anatomical structures pertinent to each individual anatomical region of the thoracic age
2.3 Detailed annotation of all normal anatomy demonstrated on each image
2.3.1 Anterior view of the thoracic cage
On the anterior view of the thoracic cage is the sternum which is made up of the Xiphoid process, corpus Sterni and the Manubrium and the ribs forming the thoracic cage. From rib one to rib seven, the ribs normally increase in size and then decreases from rib seven to rib twelve (White & Folkens, 2005). The upper seven ribs on each side of the thoracic cage distally directly connect to the sternum. Additionally, the last two ribs referred to as the floating ribs have short cartilage at their ends freely lying on the body wall sides. According to White & Folkens (2005), the basic anatomy landmark of the rib include the long shaft, neck, head and the tubercle articulating with the thoracic vertebrae as shown in Figure 9. In Figure 9 below, the ribs head are medial while the sternal ends of the ribs are lateral. The cranial edge is the side that is superior while the caudal edge is the inferior part. Each pair of the ribs in the thoracic cage posteriorly articulates with the thoracic vertebrae. Costovertebral joints are the joints where the ribs articulates with the vertebrae. Flynn (1996) pointed out that on the anterior side of the thoracic cage, only the first seven ribs directly articulates with the sternum at the costosternal joints and they are referred to as the true ribs, while the rest are referred to as the floating ribs

Figure 9
Some of the distinctive elements of the thoracic cage include the following
- The first rib is the most unusual and can be easily be identified. Is normally thick, broad and blunt and that ribs has no caudal groove as observed by Roberts & Manchester (2010).
- The second rib serves as an intermediary to the first and the third rib up to the ninth ribs that are more regular. This rib also has a tuberosity that is large for the anterior serrator muscles half way long its length
- The eleventh rib has a sternal end that is often pointed and lacks the tubercle
- The twelfth rib is shorter compared to the eleventh rib and sometimes can be even be shorter that the first rib. Moreover, it lacks the costal and the angle groove and is identifiable easily (Mary, 1999).
Sternum
The sternum is made up of the three bones; the Xiphoid process, corpus Sterni and the Manubrium. As shown in Figure 10 and 11, there are seven facets laterally locates for the anterior of thoracic cage’s true ribs alongside manubrium and sterni. The manubrium is the squarest and thickest section of the sternum bones and is easily identifiable. At the superior corners of the manubrium are the clavicular notches which articulates with the lefst and right clavicles. The scapula and the clavicles helps in forming the shoulder girdle (Hale et al, 1983).

Figure 10
Compared to the manubrium. Corpus sterni is thin and is bladelike. Moreover, there is presence of costal notches and they cover for the second to seventh rib as shown in Figure 11. Lastly, the xiphoid process is inferiorly located to the corpus sterni. Xiphoid process in the sternum shares the seventh costal north and highly variable in shape (Kenyon, 1989).
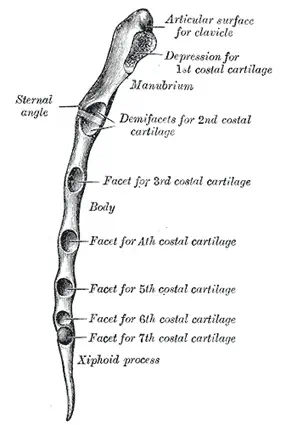
Figure 11
Costal cartilage
They make up the ribs medial portion on the anterior side to be more flexible as shown in Figure 12. The thoracic arch, which is a landmark on the surface is entirely made up of the costal cartilage.

Figure 12
Thoracic vertebrae
It runs down the posterior thoracic cage midline. Flynn (1996) indicated that the twelve thoracic vertebrae found on the posterior of the thoracic cage are regarded as part of the thoracic cage and the spinal column. Additionally, thoracic vertebrae are the only vertebrae in the spinal column with costal facets which makes sense because there is no any other kind of vertebrae which articulate with the ribs as shown in Figure 12 (Hale et al, 1983).
Case study 3: Arm skeleton
A brief justification
The bones of the hand and the arm have the critical job of providing the muscles attachment points moving the upper limb and also supporting the upper limbs. The arm skeleton was selected for this case study because these bones of the arms form joints which offer flexibility and wide range of motion that is needed to manipulate objects with the hand and arm deftly. The bones of the arms also provide strength to resist stresses and forces that are extreme and at upon the hands and arms during exercises, sports and heavy labour (Parker & Dowell, 1988).
Overview & review of the imaging protocol performed
The imaging protocol performed on the arm skeleton anatomy to best demonstrate the relevant anatomy to enable answering of the clinical question poised for the case study three. The images included different anatomical regions of the arm skeleton such as the clavicle, scapula, humerus, ulna, radius, phalanges, carpals, metacarpals and the joints. The images presented in the case study has been presented in different anatomical planes and direction. First, coronal and transverse planes are evident in the images in this case study three. Contrast media has not be used in these case study images like the way earlier case studies used the contrast media. However, some of the images in this case study used colored background to bring out the aesthetic beauty of the images. Moreover, the images has also used the line drawings to best illustrate the anatomical regions and easier understanding of the labels of the images.
Detailed annotation of all normal anatomy demonstrated on each image
The pectoral girdle which consist of the clavicles and the scapula forms the point of attachment between the arm and the chest. The clavicle is a long bone connecting the scapula to the sternum if the thoracic cage. According to Green (2006), clavicle forms two joints, that is the sternoclavicle joint formed with the sternum and the joint formed with the scapula’s acromion called acromioclavicular. The clavicle bone allows the shoulder joint to remain attached to the chest bones while moving in circles as shown in Figure 13
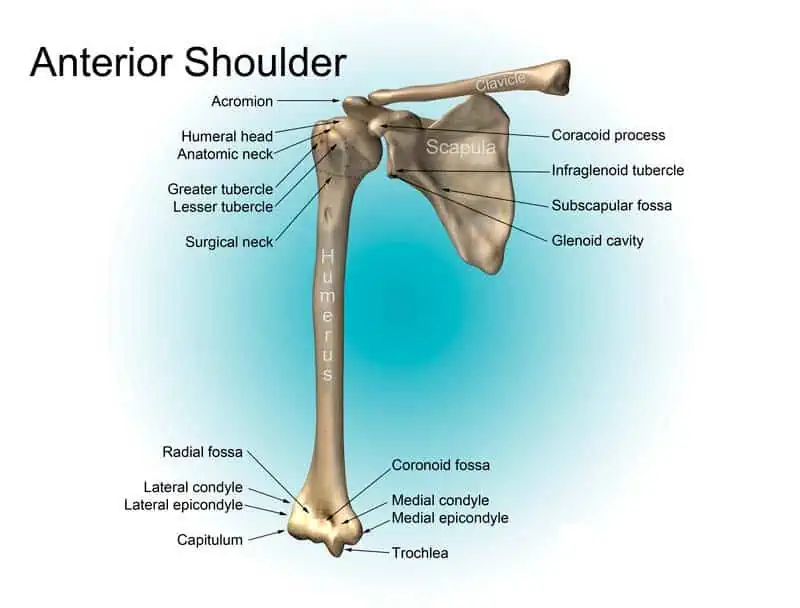
Figure 13
Scapula lies posteriorly to the clavicle and is a triangular flat bone that is located laterally to the thoracic spine in the body’s dorsal region. Parker (1989) indicated that the scapula forms two joints, that is the humeroscapular or shoulder joint with the humerus and the acromioclavicular joint with the clavicle. The glenoid cavity is situated on scapula’s lateral end and forms the socket for the shoulder joint that is ball and socket. Several muscles attach the scapula and assist in moving the shoulder as shown in Figure 13 and 14
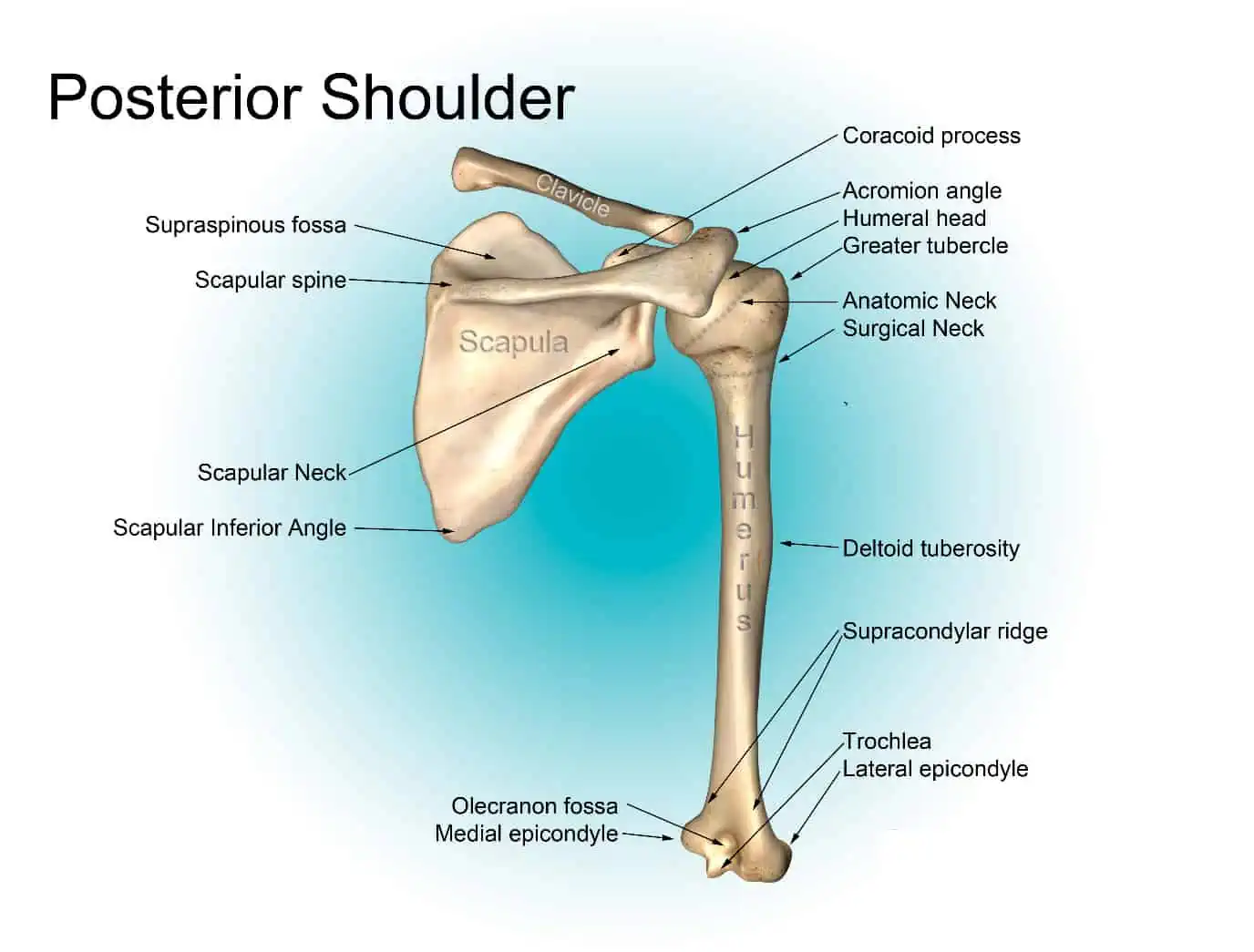
Figure 14
Parker & Dowell (1988) stated that the humerus is the only bone found in the upper arm. It is a large long bone extending from the scapula of the shoulder to the radius and ulna of the lower arm. The humerus proximal end also referred to as the head is a round structure forming the shoulder joint’s ball and socket. On the distal end of the humerus, it forms a cylindrical wide process that meets the radius and ulna to form the elbow joint’s inner hinge as shown in Figure 13, 14 and 15. The deltoid, pectoral, rotator cuff and latissimus dorsi attach to the humerus to raise, rotate and lower the shoulder joint’s lower arm.
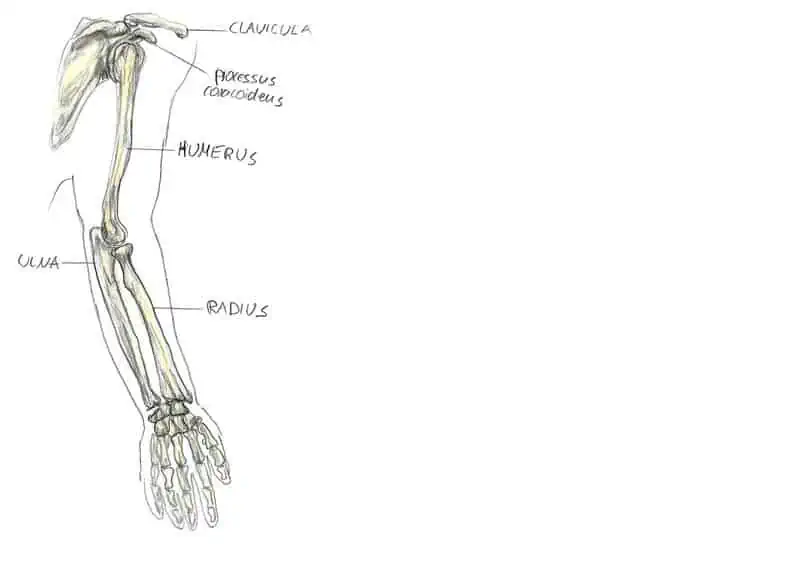
Figure 15
The forearm contains two parallel, long bones: the radius and the ulna. Between the two bones, ulna is the larger and longer residing in the medial side of the forearm. Green (2006) asserted that at the proximal of the ulna, it is widest and considerably narrows to the distal end. Furthermore, at the proximal end of ulna, it forms the elbow joint hinge with the humerus. Olecranon is the ulna’s end and it extends past the humerus forming the elbow’s bony tip. Ulna bone also forms a wrist joint at its distal end with the carpals and the radius as shown in Figure 15 and 16

Figure 16
When comparison is made to the ulna, the radius is slightly thinner, shorter and located at the forearms medial side. The radius bone at the elbow is narrowest and widens as it is extending towards the wrist. The radius rounded head at its proximal end forms the pivoting pint at the joint of the elbow that allows lower arm and hand rotation. Additionally, the radius at its distal end is much wider compared to the ulna and forms the wrist joint bulk with the carpals and the ulna (Parker, 1989). The radius distal end also rates around the ulna wen the forearm and hand rotate as shown in Figure 17

Figure 17
Parker & Dowell (1988) pointed out that despite the hand being such a small body region, it contains 27 tiny bones and many joints that are flexible.
- The carpals are collection of eight bones that are cube shaped roughly in the hand’s proximal end. Together with radius and ulna, they form the wrist joint and also forms joints with the palms metacarpals. Green (2006) asserted that carpals forms many small joints that are gliding with each other to provide extra flexibility to the hand and wrist as shown in Figure 17 and 18
- The five cylindrical, long metacarpals forms the palms supporting bones of the hand. Every metacarpal forms a joint with proximal phalanx of a finger and another joint with the carpals. Parker (1989) indicated that metacarpals have the ability of abducting to spread the palm and fingers apart and can also adduct to bring the palm and the fingers together. Additionally, metacarpals provide flexibility to the hand when touching the thumb, gripping an object and when pinkly fingers together as shown in Figure 16 and 18.
- The phalanges according to Parker & Dowell (1988), are a collection of 14 bones that move and supports the digits. Every digit has three phalanges that is the distal, middle and the proximal, except the thumb which only has the distal phalanx and the proximal phalanx. Green (2006) defined phalanges as long bones forming hinge joints between themselves and also the oval (condyloid) joints with the metacarpals. These joints allows the extension, flexion, abduction and adduction of the digits as shown in Figure 16, 17 and 18

Figure 18
Case study 4: The human Heart anatomy
A brief justification
The heart is a muscular body organ that operates as the circulatory pump of the body. The heart is located posterior to the sternum and medial to the lungs in the thoracic cavity (Boyd, 2003). The heart was chosen for this case study for its significance to the human body’s circulatory system. According to Lapatza et al (1994), the heart takes the deoxygenated blood in through the veins and then deliver it to the lungs where it is oxygenated before pumping it back into different arteries. These arteries provide nutrients and oxygen to the tissues of the body by transporting the oxygenated blood throughout the body.
Perin (1983) indicated that at the superior end of the heart is attached to the pulmonary vein, aorta and vena cava. On the other hand, the apex or the heart’s inferior tip just rests to the superior of the diaphragm. The heart’s base is situated along the midline of the body with its apex pointing to the left side. Therefore, given that the heart points towards the left side, about two-thirds of the mass of the heart is found on the body’s left side and the other one-third is found to the right.
Overview & review of the imaging protocol performed
The heart organ discussed in this case is entirely made of cardiac muscles. Therefore, to different anatomical parts, the images presented in this case study used contrast media where the images were presented in different colours. In all the images of the heart in this case study, the part of the heart that transports the deoxygenated blood are painted in blue colour whereas the sections of the heart that transports the oxygenated blood has been indicated by the red colour. These contrasting colours used in the imaging protocol has been performed to best demonstrate the relevant anatomy to enable answering of the clinical question poised for the case. The images have been presented in coronal plane where anterior and posterior view of the heart has been presented. The major anatomical regions covered on the coronal plane include the major blood vessels of the heart, the chambers and surface features. On the images that shows the internal parts of the heart, anatomical structures include the internal muscles, valves and the vessels
Detailed annotation of all normal anatomy demonstrated on each image
Anterior and posterior view
The anterior and posterior view of the heart shows the organ lying in the coronal plane. The anatomical structures found on the anterior side of the heart are many. This section will annotate some of these anatomical structures of the heart (Boyd, 2003).
The pericardium which is a double walled sac encases the heart and it functions to protect the heart in addition to anchoring it within the chest region. The outer wall of the heart comprises of three layers: pericardium or the outermost wall layer, myocardium or the middle layer which contains the contracting muscles, and the endocardium or the inner layer which is the lining in contact with the blood (Boyd, 2003).
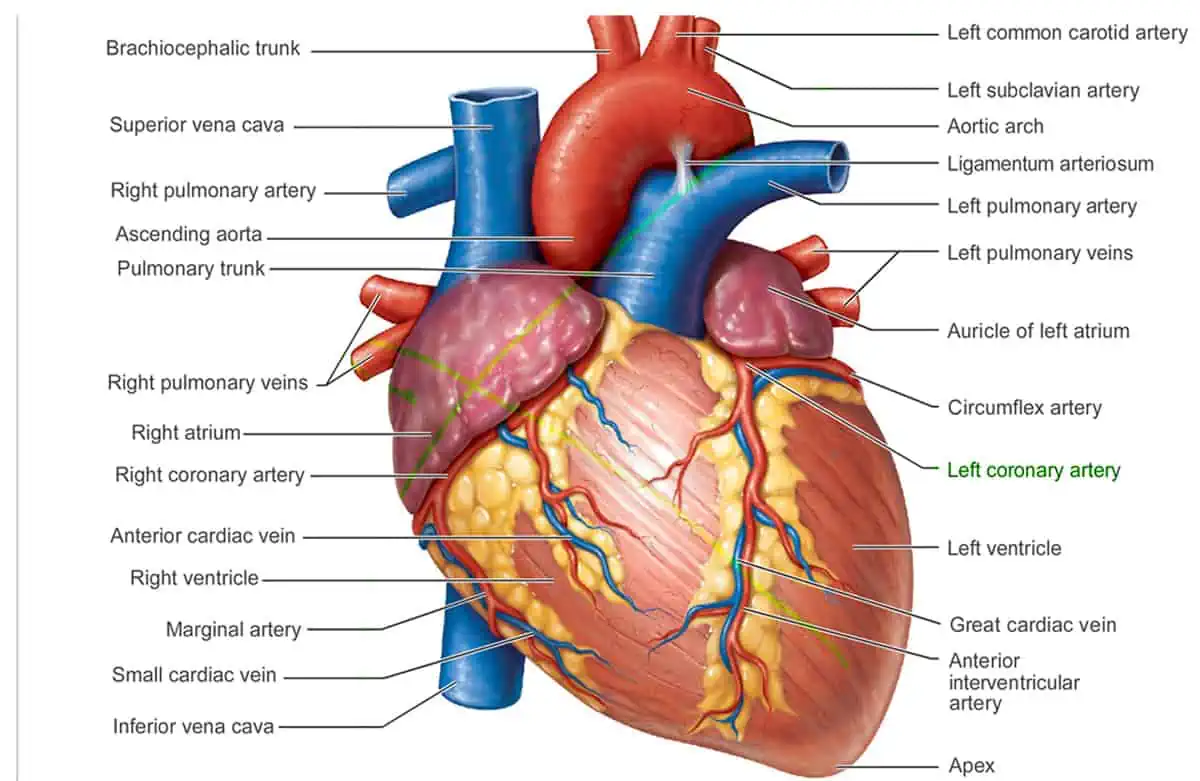
Figure 19
Coronary arteries- These are network of blood vessels that carry nutrient and oxygen rich blood to the cardiac muscle tissue. The heart muscles according to Lapatza et al (1994) is primarily composed of cardiac muscle tissue that contract and relax continuously and therefore must have supply of nutrients and oxygen constantly. The blood that leaves the left ventricle of the heart exits through the aorta, the main artery of the body. The two major coronary arteries known as the right and left coronary arteries emerge near the top of the heart from the beginning of the aorta the left main coronary which is the initial left coronary artery segment branches into two smaller arteries: the left circumflex coronary artery and the left anterior descending coronary artery which is embedded on the hearts front side on the surface. On the other hand, the left circumflex coronary artery is embedded on the hearts surface at the posterior side of the heart and circulates on the hearts left side
Perin (1983) pointed out that the coronary arteries progressively branch into smaller vessels which penetrate the heart muscles. The capillaries, which are the smallest branches are so narrow that only allows the red blood cells to travel only in single file
Superior vena cava- Is one of the major veins that brings de-oxygenated blood to the heart from the body. The veins from the upper body parts and the head feeds into the superior vena cava and then are emptied into the hearts right atrium.
Inferior vena cava- It is one of the major veins that brings de-oxygenated blood to the heart from the body. The veins from the lower torso and the legs feed into the inferior vena cava and then are emptied into the hearts right atrium.
Coronary sinuses– they collect the draining blood from the myocardium.
Aorta- It is the single largest blood vessel in the human body. The vessel carries blood that is rich in oxygen from the left ventricle to different body parts (Boyd, 2003).
Pulmonary artery-It is the vessel that transports de-oxygenated blood to the lungs from the right ventricle
Pulmonary vein– it is the vessel that transport blood that is rich in oxygen from the lungs to the left atrium
Right Atrium– it receives blood that is de-oxygenated from the body from both superior and inferior vena cava. It also allows the collected deoxygenated blood to flow into the right ventricle
Right Ventricle– it receives blood that is deoxygenated from the right atrium as it contracts. Moreover, it pumps the blood towards the lungs through the pulmonary vein
Left atrium– it receives blood that is oxygenated from the lungs through the pulmonary vein. It also passes the oxygenated blood to the left ventricle (Lapatza et al, 1994).
Left ventricle- it receives blood that is oxygenated as the left atrium contracts. The left ventricles contract when it is full with blood allowing the blood to flow throughout the body through aorta. The ventricles (right and left) of the heart are the discharging chambers or the hearts actual pumps. Compare to the atria, the ventricles’ walls are larger and upon contraction, they propel blood into circulation out of the heart. The right ventricle of the heart pumps blood into the pulmonary human trunk, which directs the blood to the lungs for gaseous exchange (Lapatza et al, 1994).

Figure 20
The human heart has four cambers, which is the two inferior ventricles and the two superior atria. The inter-atrial septum is an internal partition dividing the heart longitudinally and the inter-ventricular septum separates the ventricles. Perin (1983) stated that the right ventricle of the heart forms the most of hearts anterior surface whereas the heart apex is formed by the left ventricle.
On the surfaces of the heart, two grooves indicates the heart’s four chambers. The atrioventricular groove also referred to as the coronary sulcus encircles the atria and ventricles junction like the crown. Similarly, the anterior interventriculae sulcus marks the septum anterior position and cradles the anterior interventriculae artery where the left and right ventricles separate. This continues as the posterior interventriculae sulcus, that marks a similar position on the surface of the poseroinferior. Auricles are the only surface feature found on every atrium and it is wrinkled, small appendage (Boyd, 2003).
Internal view of the heart
Internally in the heart, the right atrium of the heart has two basic parts: that is a smooth anterior and posterior portion in which muscle tissue bundles form ridges on the wall. These bundles of muscles are referred to as the pectinate muscles. The anterior and posterior region of the right atrium are separated by crista terminalis, which is a C-shaped ridge. Contrastingly, the left atrium is almost wholly smooth and the auricle is the only region with pectinate muscles additionally, the interatrial septum has a shallow depression referred to as the fossa ovalis, which marks the spot where foramen ovale, an opening, existed in heart of a foetus. This opening closes after birth (Lapatza et al, 1994).
The irregular muscle ridges referred to as the trabeculae carneae mark the ventricular chambers inner walls. Moreover, the papillary muscles which is another bundles of muscles project into the cavity of the ventricles and play a role in function of the valve

Figure 21
Heart valves
The heart has four valves which enforce one way traffic of blood flow. The atrioventricular (AV) valves are two and prevent backflow of blood into the atria chamber when the ventricles pump or contracts. The tricuspid valve or the right AV valve has three cusps which are flexible whereas the mitral valve or the left AV valve or the bicuspid valve has two cusps. Chordae tedineae are collagen chords that are attached to each flap of AV valve, and they help in anchoring the cusps to the papillary muscles. Perin (1983) indicated that the papillary muscles and the chordae tendineae serve anchorage wires to the valve flaps during their closed positions as shown in Figure 22

Figure 22
Semilunar (SL) valves– the pulmonary and aortic semilunar valves guard largest arteries bases that stem from the ventricles and prevent backflow into the respective ventricles. Each valve has crescent moon shaped three cusps. The SL valves open and close due to pressure differences as shown in Figure 23


Figure 23
Case study 5: kidney anatomy
A brief justification
Kidneys are body organs that filters and dispose wastes from the body system. The kidney organ was selected for this case study because about a third of the blood that leaves the blood passes through it for filtration before flowing to the entire tissues of the body. Kidney organs are very vital to the human body to the point that any of them could result to rapid waste accumulation and even death. Kidney are found in pairs and located along the abdominal cavity’s posterior muscular wall. Brenner & Rector (1991) pointed out that the left kidney is slightly located superiorly than the right kidney because of the liver’s larger size on the right hand side of the body. Additionally, it lies behind the peritoneum lining the abdominal cavity. The perirenal fat, an adipose tissue surrounds the kidney organs and act as a padding for protection. Other reasons why kidney was chosen for the case study because of its further significant functions of electrolytes regulation, fluid regulation, acid-base balance and stimulation of production of the red blood cells. Moreover, kidneys serve in regulation of blood pressure through the renin-angiotensin-aldosterone system where it controls water reabsorption and intravascular volume maintenance. Lastly, kidney are very important as an anatomical organ since it reabsorbs amino acids and glucose in addition to having hormonal functions via vitamin D, calcitriol and erythropoietin activation (Resnick & Parker, 1982).
Overview & review of the imaging protocol performed
The selected images used in this case study has been presented in unique imaging protocol so as to bring out the relevant and distinctive anatomical parts of the kidney to enable answering the poised clinical questions presented in the case study. Majorly the images in this case study focused on the internal part of the kidney in sagittal plain and also slightly on the external features of the veins and arteries that connect with the kidneys. The key anatomical regions of the kidney presented in the images include the internal parts such as the kidney pelvis, cortex, blood vessels and tubules. Additionally, the nephron of the kidney and its anatomical structures have been shown. The most notable imaging protocol in the images is the contrasting colours used in the images to indicate different structures of the kidney.
Detailed annotation of all normal anatomy demonstrated on each image
The kidney organs are bean shaped with the concave side located medially and the convex side laterally located. The renal hilus, or the indented concave side of the kidney provides space for the ureter, renal vein and renal artery to enter the kidney as shown in Figure 24 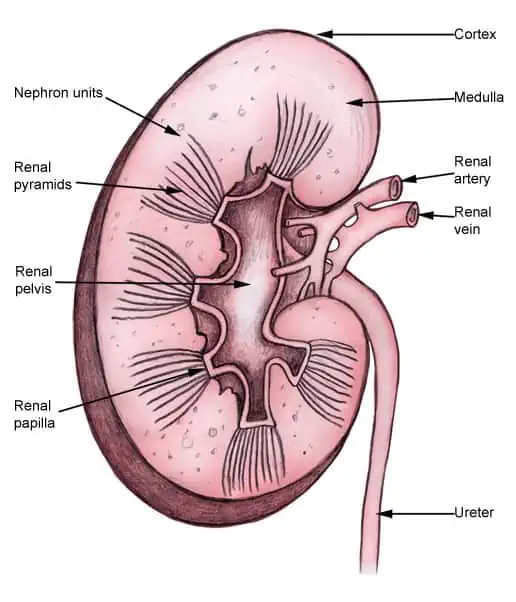
Figure 24
Sagittal plane
The thin fibrous connective tissue layer forms the surrounding renal capsule for every kidney. Graves (1971) stated that the renal capsule of the kidney provides the outer shell that is stiff to maintain the shape of the inner tissues that are soft as shown in Figure 25
Dense, soft vascular renal cortex are found deep in the renal capsule. The renal medulla is formed by seven cone shaped pyramids deep to the renal cortex. These renal pyramids are aligned with their apexes pointing inwardly toward the kidney’s centre, and their bases outwardly facing toward the renal cortex.
Each apex is connected to the minor carylx, which is a small hollow tube collecting urine. Kinne (1989) stated that the minor calyces then merge forming three larger and major calyces that also further merge forming the hollow renal pelvis and the kidney’s centre. The renal hilus, is the section which the renal pelvis exits, where the urine flows into the ureter.

Figure 25
The anatomy for the kidney’s blood supply is a network of both veins and arteries within the kidney organ. The renal arteries directly branching from the abdominal aorta enters into the kidneys via the renal hilus. The renal arteries inside the kidneys then diverge into afferent smaller arterioles of the kidneys. The afferent arterioles are connected to the renal cortex where they carry blood and separates into capillaries bundle referred to as the glomerulus. The blood recollects from the glomerulus into smaller efferent arterioles descending into the renal medulla. The renal tubules are surrounded by the peritubular capillaries which separated from the efferent arterioles. The peritubular capillaries merges to form veins which also further merge forming the larger renal vein, which exist the kidney and joining the inferior vena cava (Brenner & Rector, 1991).
The nephron
These are microscopic functional units of the kidney that filters blood to produce urine as waste. There are two main parts of the nephron: renal tubule and the renal corpuscle. The renal corpuscle is responsible for blood filtration and is formed by the glomerulus capillaries and the glomerular capsule or the Bowman’s capsule. Resnick & Parker (1982) indicated that the glomerulus is a bundled capillaries network that increases the blood surface area that is in contact with the walls of blood vessels. Glomerular capsule, which is a cup-shaped simple squamous epithelium which is double layered with a hollow space in between the layers, surrounds glomerulus. Podocytes which are special epithelial cells form glomerular capsule layer surrounding glomerulus capillaries. Podocytes work in conjunction with the capillaries’ endothelium to form a thin filter that separates urine from the blood that passes through the glomerulus. The glomerular capsule’s outer layer holds the separated urine from the blood within the capsule. Graves (1971) pointed out that at the glomerular capsule’s far end, opposite the glomerulus, is the renal tubule mouth
Series of tubes known as the renal tubule recover solutes that are non-waste from urine by concentrating urine. The renal tubule of the nephron carries urine to the renal pelvis from the glomerular capsule as shown in Figure 26

Figure 26
Case study 6: Liver anatomy
A brief justification
Liver organ is the second largest body organ and weighs about three pounds after the skin. The liver was selected for the case study because it performs several essential functions that are related to metabolism, digestion, storage of nutrients and immunity within the body hence making it a vital organ. These functions of the liver make it important without which the human body will die because of lack of nutrients and energy (Ryū, & Cho, 2009).
Overview & review of the imaging protocol performed
The three images used in this case study of the liver has applied contrast media to clearly show both external and internal anatomical structure of the liver. Clear presentation of the images has been done best demonstrate the relevant anatomy to enable answering of the clinical question poised for the case. The images presented the liver in the frontal plane which showed the anterior and posterior parts. Moreover, internal anatomical structure have also been shown. Some of the anatomical regions shown include the blood vessels, the four lobes, and the bile ducts among other minor anatomical regions
Detailed annotation of all normal anatomy demonstrated on each image
Frontal plane
The liver organ is grossly triangular extending across the whole abdominal cavity below the diaphragm. The liver is made of pinkish-brown very soft tissues that are encapsulated by a capsule of the connective tissue. The capsule is further reinforced and covered by the abdominal cavity’s peritoneum, which hold it in place and protects it within the abdomen (Gadžijev & Ravnik, 1996).
The peritoneum of the abdominal cavity connects the liver organ into four locations: the right and left triangular ligaments, coronary ligament and the falciform ligament. Self (2009) stated that the connections are not true or normal ligaments anatomically but are just peritoneal membrane regions that are condensed that supports the liver.
The liver is made up of four different and distinct lobes: quadrate, caudate, right and left lobes. The right and the left lobes are the largest and are separated by the falciform ligament. The caudate lobe that is small extends posteriorly of the right lobe wrapping around the inferior vena cava. Moreover, the quadrate lobe which is also small is inferior to the caudate lobe, extending posteriorly to the right lobe and wrapping around the gall bladder as shown in Figure 27
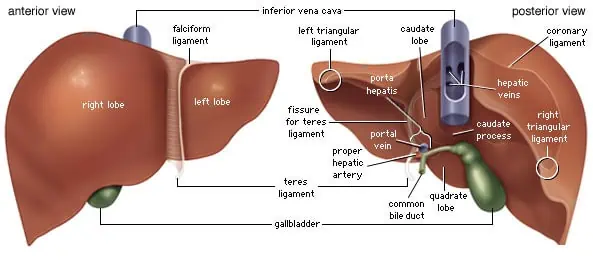
Figure 27
The bile ducts
These are tubes which carry bile through the gallbladder and liver and they form a biliary tree, which is a branched structure. Bile canaliculi are microscopic canals that join together to form many bile ducts, which also join together to form larger right and left hepatic ducts. These two hepatic ducts also join and form common hepatic duct which drains all the bile from the liver. Glisson et al (1994) pointed out that the common hepatic duct eventually joins the cystic duct which is from the gall bladder forming the common bile duct as shown in Figure 28.
Blood vessels
Because of the hepatic portal system, blood collected in the hepatic portal vein from the capillaries of the pancreas, stomach and spleen is delivered to the liver tissues where its contents are subdivided into smaller vessels and then processed before passing to the entire body. The blood that leaves the liver tissues collects in the hepatic veins leading to the vena cava and then heart. Additionally, the liver organ has its own arteries and arterioles system which provide its tissues with the oxygenated blood (Ryū & Cho, 2009).

Figure 28
Lobules
These are small hexagonal functional units found in the livers internal structure. Each lobule comprises of the central vein that is surrounded by six hepatic arteries and six hepatic portal veins. Sinusoids are capillary like tubes that connect these blood vessels, and extends from the arteries and portal veins to meet the central vein (Gadžijev & Ravnik, 1996).
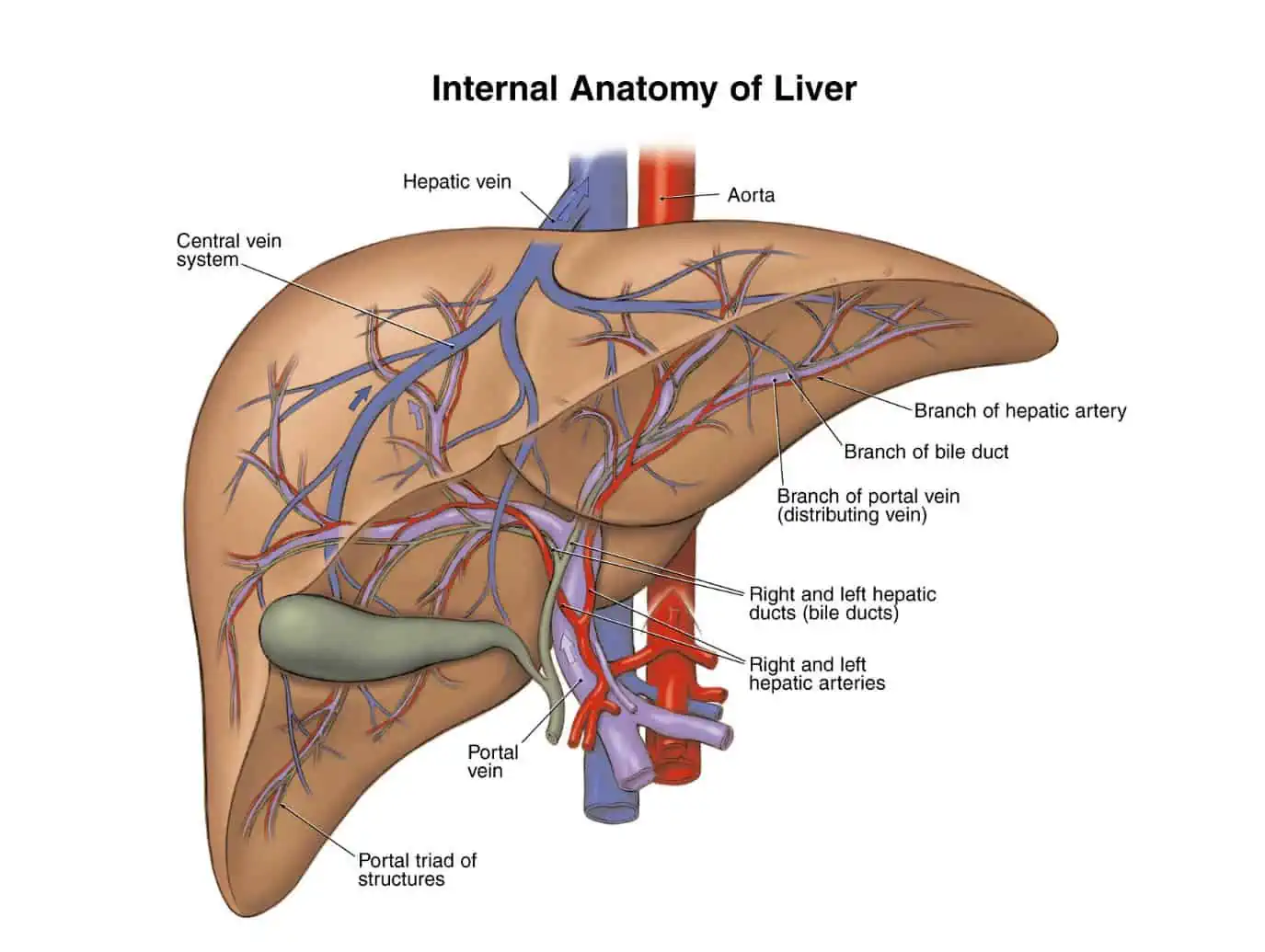
Figure 29
Case study 7: stomach anatomy
A brief justification
In the human body, stomach is the main storage tank of food. The stomach organ was chosen as a case study because of its significance to the body and the digestion system. Were it not for the storage capacity of the tank, then human beings would have to constantly eat. The stomach is also important in that it secretes digestive enzymes, mucus and mixture of acid that helps in the sanitization and digestion of the food while still in the stomach (Templeton, 1964)
Overview & review of the imaging protocol performed
Different images has been presented for this case study to better illustrate the anatomy of the stomach. First, contrast media has been applied to better bring out the frontal plane of the stomach’s different regions. Moreover, other images have used colours in the 3-D images to better elaborate on the layers of the stomach organ. Different anatomical regions has been shown in the diagrams and labelled in the images that are in the frontal plane. Some of the major anatomical regions presented include the fundus, cardia, body, and pylorus. Internally, the major anatomical regions include the rugae of mucosa, the pyloric canal, serosa and muscularis.
Detailed annotation of all normal anatomy demonstrated on each image
Anterior view
Stomach organ is rounded and hollow and is located inferior to the diaphragm to the abdominal cavity’s left part. The stomach is located between the duodenum and oesophagus and is roughly crescent shaped gastrointestinal tract enlargement as shown in Figure 30.

Figure 30
The stomach’s inner layer has many wrinkles known as gastric folds or rugae which allows the stomach the stomach to expand and stretch so as to accommodate large meals in addition to helping in gripping and moving food during the process of digestion (Agur et al, 1999).
Based on function and shape, the stomach organ can be classified into four regions according to Wolf-Heidegger & Köpf-Maier (2006) as shown in Figure 30 above:
- The oesophagus that connects to the stomach at cardia, which is tube-like narrow region opening up into wider regions of the stomach. Lower Oesophageal sphincter located within the cardia, is a bundle of muscle tissue contracting to hold acid and food inside of the stomach.
- The body of the stomach connects with the cardia and it forms the largest and central region of the stomach
- Fundus is superior to the body and has a shape of dome
- Pylorus is a funnel shaped region and is inferior to the body. The pylorus connects duodenum to the stomach and also contains the pyloric sphincter which controls the flow of chime or partially digested food out of the stomach to the duodenum.
Microscopic view of the stomach
Microscopic imaging of the stomach organ structures shows that it is made of multiple, distinct tissue layers: serosa, muscularis, sub-mucosa and mucosa layers as shown in Figure 31
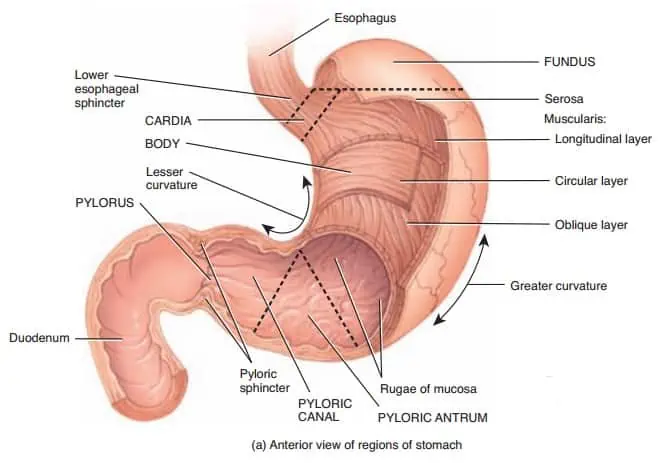
Figure 31
The mucosa is the stomach’s innermost layer made up of the mucous membrane. The stomach’s mucous membrane has simple columnar epithelium tissue with several exocrine cells. Muscularis mucosae is a thin layer of smooth muscle found deep inside the mucosa. The muscularis mucosae layer permits mucosa to form folds and also to increase its contact with the contents of the stomach (Templeton, 1964).
Sub-mucosa layer of the stomach surrounds the mucosa and is made up of different blood vessels, connective tissues, and nerves. The connective tissues of the submucosa supports the mucosa tissues and also connects it to the muscularis layer. Additionally, the supply of blood of the submucosa provides the stomach wall some nutrients (Agur et al, 1999).
The stomach’s muscularis layer surrounds the submucosa and forms the large amount of the mass of the stomach. Wolf-Heidegger & Köpf-Maier (2006) pointed out that the muscularis is made up of three smooth muscle tissue layers arranged with its fibres running in three different directions. These smooth muscle layers allow the stomach to contract, mix and move the food through the digestive tract.
Serosa is the stomach’s outermost layer surrounding the muscularis layer. Templeton (1964) defined serosa as a thin serous membrane that is made up of areolar connective tissue and the simple squamous epithelial tissue. Serosa has a slippery, smooth surface and secrets the serous fluid. The wet, smooth surface of serosa helps in protecting the stomach from friction wen the stomach is expanding with the food and also moves to churn and mix and propel the chime

Figure 32
Case study 8: Muscles of the arm and the Hand
A brief justification
The muscles found on the hand and the arm is designed specifically to meet the diverse needs of the body speed, strength and precision while completing several complex daily duties. This case study choose muscles of the arms and the hand because daily activities such as lifting heavy load such as the boxes and other weights requires arm muscles brute strength. Similarly, typing, paining and writing all require precision and speed from the same arm and hand muscles (Liberace, Lubkin, & Liberace Studio (Firm), 2013).
Overview & review of the imaging protocol performed
The imaging protocol performed in case study six varies depending on the image. Some of the imaging techniques applied in the images of this case study include use of the contrast colour images, line diagrams and CT scans that provided computerised images. all these techniques used in the imaging protocol has been applied to bring out the relevant anatomical regions in the arm and the hand body parts to enable answering of the clinical questions for the case study six. The images provided clear and distinct anatomical regions of the arm and the hand such as the upper arm muscles, shoulder muscles, forearm muscles and hand muscles that are relevant for the case. Moreover, the images are presented in different anatomical planes such as the frontal, and sagittal planes. Similarly, the images of the forearm have been presented in both posterior and anterior views to get better view of the inner muscles located in the arm and the forearm. However, these images as much as some of them were coloured, they lacked contrast colours to better distinguish specific muscles in a muscle group. For instance, in the triceps branchii, the image needs contrast media to distinguish individual muscles that comprise triceps branchi for clearer view.
Detailed annotation of all normal anatomy demonstrated on each image
The arm in human anatomy is the upper limb comprising of the body regions between the elbow joint and the glunohumeral joint (Chung & Steinbach, 2010). However, the arm is commonly used to refer to the arm and also the hand. The arm and the hand comprises of the upper arm, the forearm and the hand. Doyle & Botte (2003) indicated that anatomically, shoulder girdle is considered part of the arm. The muscles of the arm and hand are divided into anterior and posterior components. Moreover, other muscles also considered to be part of the arm include the deltoid muscle which has part of itself in the anterior compartment if the arm. The deltoid muscles extends over the shoulder is the major abductor muscle found in the upper limb. Another muscle is the branchioradialits muscle which originates from the arm and insert into the forearm. This muscle is responsible for supination or the rotation of the hand so that the palm can face forward as shown in Figure 33

Figure 33
The upper arm muscles are responsible for the extension and flexion of the forearm at the elbow joint. Liberace, Lubkin & Liberace Studio, (2013) indicated that forearm flexion is achieved by a three muscle group: the branchioradialis, biceps branchii and the branchialis. These flexor muscles are found on the upper arm anterior side and extend from the scapula and humerus to the radius and ulna of the forearm. In addition, the biceps branchii functions as forearm supinator by moving the palm of the hand and rotating the radius anteriorly as shown in Figure 34. The triceps branchi are located on the posterior side of the upper arm and it acts as the forearm extensor at the shoulder humerus and the elbow. As the name indicates, biceps branchii has three heads which originates from the scapula and the humerus. The three heads then merge and insert on the ulna’s olecranon as shown in Figure 34.

Figure 34
Chung & Steinbach (2010) pointed out that most of the muscles moving the fingers, hand and wrist are located on the forearm. These strap-like, thin muscles extend from the radius, ulna and humerus and insert into the carpals, phalanges and the metacarpals via long tendons as sown in Figure 35. The muscles located on forearm anterior side such as the flexor digitorum superficialis and the flexor carp radialis, forms the groups of flexor that flexes the hand as the wrists joints and each and every phalanges. Doyle & Botte (2003) indicated that the tendons of these muscles goes through a small corridor found in the wrist referred to as the carpal tunnels as shown in Figure 35
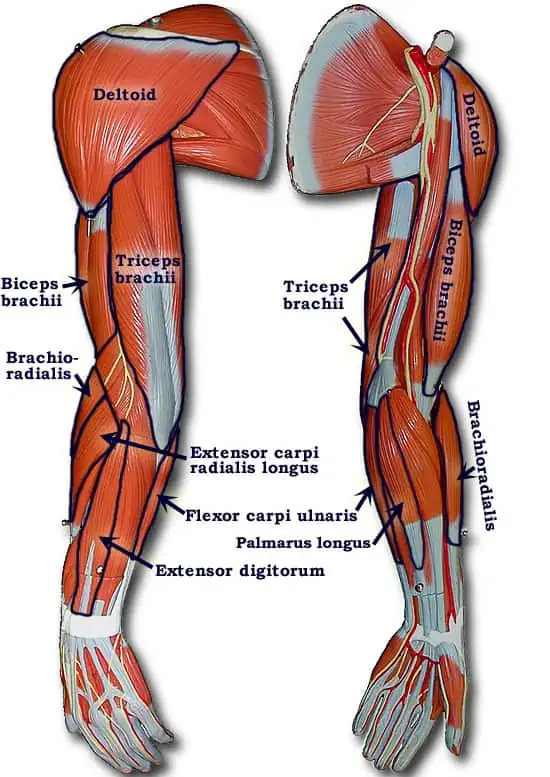
Figure 35
The extensor muscles on the posterior side of the arm such as the extensor digitorum, extensor carpi act as the antagonists to the flexor muscles found on the anterior side of the arm by extending the fingers and the hand. The extensor muscles run as thin, long straps from the humerus to the metacarpals and the phalanges as shown in Figure 36. Generally, extensors are somewhat weaker compared to the flexor muscles that they antagonize, because of the ease in opening a hand than gripping something firmly (Liberace, Lubkin & Liberace Studio, 2013).

Figure 36
Case study 9: Muscles of the leg and the Foot
A brief justification
Propelling, balancing and supporting of the human body is the work of the leg and foot’s muscular system. From the string and large muscles of the legs and buttocks to the fine, tiny muscles of the toes and feet, these muscles has the ability of exerting tremendous power while making small adjustments constantly for balance. This anatomical region of the human body was chosen for the case study because of the leg and foot muscles’ importance for the human movement and daily functions. It is the presence of the legs that human beings are able to be mobile and explore the environment for its own survival (Behnke & Donnelly, 2001).
Overview & review of the imaging protocol performed
The images of muscles of the leg and the foot of this case study has been presented in frontal anatomical plane. Moreover, different anatomical directions has been applied in the imaging of the case study leg muscles such as the frontal, lateral, posterior and superior anatomical directions. The anatomical structures of the muscles of the leg has been labelled in the diagrams for easier comprehension. Major anatomical structures identified include the quadriceps, hamstrings, soleus, gluteus muscle, Achilles tendon and the gastrocnemius. A contrast media particularly of colored imaging was also helpful especially in bringing out different anatomical parts in the muscles of the leg.
Detailed annotation of all normal anatomy demonstrated on each image
Anterior view and Posterior view
The anterior muscles of the leg such as the iliopsoas, quadriceps femoris and Sartorius function as a group to flex the hip thigh and also extend the knee as the knee joint. The posterior muscles such as the gluteus Maximus and hamstrings produce the opposite motion to the anterior muscles. That is thigh extension at the hip joint and leg flexion at the knee joint. The lateral muscles like the gluteus medius abduct the thigh region at the hip joint while the muscles of the medial groin adduct the thigh. These leg muscles elaborated provide powerful contractions to make the body move and also make fine adjustments for maintenance of the body posture and balance (Draves & Zelichowski, 1986).

Figure 37
On the lower part of the leg and the foot, there are a number of muscles that are located inferiorly to the leg and move the toes, foot and ankle. The muscles of the calf including soleus and gastrocnemius join and form the Achilles (calcaneal) tendon to the heel and also attach to the heel’s calcaneus bone. Shin muscles such as the extensor digitorium longus and tibialis anterior extends the toes and dorsiflex the foot. Additionally, the calf muscles subtly work to stabilize the foot and ankle joint so as to maintain the body balance (Gresczyk, 1967).
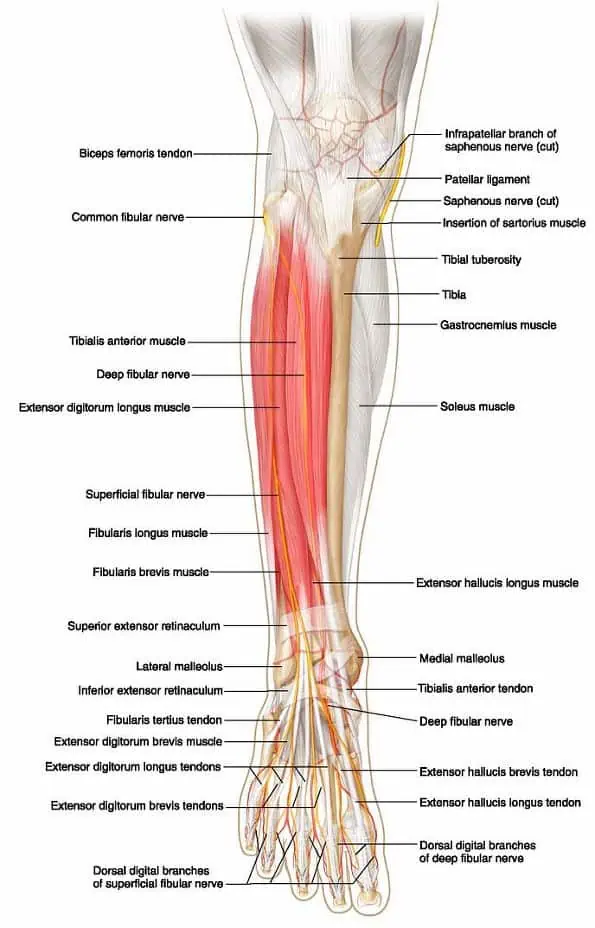
Figure 38
The largest leg muscles are present in the calf and thigh.
Quadriceps
Are the leanest and the strongest muscles in the body (MacConaill & Basmajian, 1969).quadriceps which is located on the front of the thigh is made up of four muscles and are the major knee extensors. They include:
- Vastus lateralis: it is the largest among the quadriceps and is located outside the thigh. In addition, it extends to the kneecap from the top of the femur.
- Vastus medialis-it is a muscle of the inner thigh that is tear dropped shaped and it attaches along the femur bone to the kneecap’s inner border
- Vastus intermedius– it is the deepest among the quadriceps and it lies between vastus lateralis and vastus medailis
- Rectus femoris– this muscle amongst the quadriceps it has the least effect on knee flexing and it attaches to the kneecap (Parker, 2004).

Figure 39
Hamstrings
These are the three muscles located at the back of the thigh and affect the movement of the knee and hip. They originate under the gluteus Maximus and attach to the knee to the tibia. They include:
- Biceps femoris– it is a long muscle that flexes the knee. It starts in the thigh area extending to the fibula head near the knee. It originates from ischium and back of femur. These fibres from two origins then joins and get attached to the head of tibia and fibula.
- Semitendinosus- it flexes the knee and extends the thigh
- Semimembranosus– this is a long muscle extending to the tibia from the pelvis. It flexes the knee, extends the thigh and helps in the rotation of the tibia (Behnke & Donnelly, 2001).
The muscles of the calf are significant to the toes, foot and ankle movement. Some of the major calf muscles include:
- Gastrocnemius (calf muscle) – it is one of the leg’s largest muscles connecting to the heel. It extends and flexes the foot, knee and ankle. This muscle originates from the back of femur and patella and join soleus and then get attached to the Achilles tendon at the heel
- Soleus– this muscle extends to the heel from the back of the knee. It is important in standing and walking
- Plantaris– the function of this thin, small muscle is superseded by the gastrocnemius muscles (Draves & Zelichowski, 1986).
Achilles tendon is the most important tendon found in the leg in terms of mobility. This tendon is located at the back of ankle and calf and connects the soleus, gastrocnemius and plantaris muscles to the heel bone (Gresczyk, 1967).

Figure 40
Adductor– are also referred to as the inner thigh muscles and they draw the body towards the median line. In the human thighs, there are three adductor muscles that are powerful and they include adductor longus, adductor Magnus and adductor brevis. These ribbon like muscles originate from the ischium and pubis which the pelvis lower portions and attach to the femur. Adductors muscles squeeze the thigh together and aid in flexion and rotation of the thigh (MacConaill & Basmajian, 1969).
Tibialis anterior– is a muscle strip that makes up the shin and assist in flexing the ankle to move the foot towards the knee.
Sartorius muscle-is ribbon like, narrow and long thigh muscle that begins at the pelvic girdle’s crest and obliquely extend down the front side and insert to the upper and inner portion of the tibia. It flexes the leg and thigh at the knee and outward femur rotation (Parker, 2004).
Figure 41 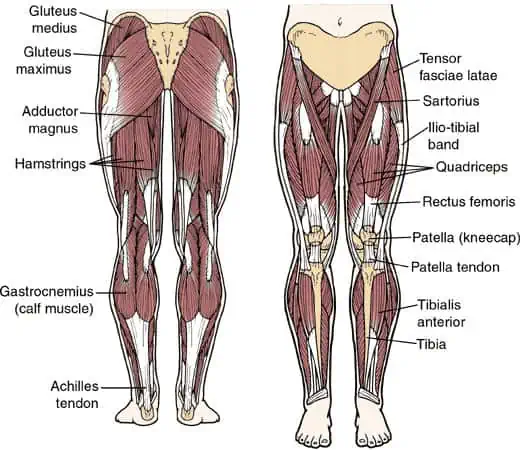
Gluteus muscle– it is the fleshy, large buttocks muscles that stretch from the pelvic girdle back portion down to the greater trochanter, which is the bony protuberance on femurs top. The gluteus muscle consists of three muscles which include:
- Gluteus maximus –is the thick, wide and large muscle at the buttocks surface originating at the ilium and the positions of the coccyx and sacrum. Its major functions is thigh extension such as climbing, running and arising from the sitting position. Moreover, it rotates the thigh outward (Behnke & Donnelly, 2001).
- Gluteus medius-is directly located under the gluteus Maximus and originates at the back of the ilium and stretches downward to the femur’s greater trochanter.
- Glueteus minimus– is located under the gluteus medius and also begin at the ilium and get attached to the femur. Gluteus minimus and gluteus medius abduct the thigh that is laterally pull away from the body’s midline. Additionally, they help in rotating inward the thigh (Draves & Zelichowski, 1986).
Case study 10: muscles of the hip
A brief justification
The human hip joint is one of the joints that is most flexible n the whole human body. The many hip muscles provide stability, strength and movement to the bones of the thigh and hip and the joint itself. These hip muscles can be categorised based upon their function and location. The hip muscles were chosen for this case study because the hip is the major joint that bears weight. Bearing of the body weight stress the hip when walking, running or jumping or even at rest. These large and strong hip muscles which move and support the hip is the major focus for this case study (Brungardt et al, 2006).
Overview & review of the imaging protocol performed
The imaging protocol used in this study varied to give a clear view of different anatomical planes, labels and directions of the hip muscles. First, the images has been taken from different views which included anterior and posterior view of the hip muscles at the thigh region. The views of the images in this case study were also taken at different angles sequentially in anterior oblique positions. The images of this case study also indicate that the subjects were standing in erect positions. The images are presented in different anatomical planes such as sagittal and frontal planes. The anatomical regions of the images are labelled clearly in each image for distinction. Contrast media were also used in the images to help in distinguishing key anatomical structures pertinent to each individual anatomical region of the hip muscles. Some of the anatomical regions identified has been grouped into four major muscles groups which include: the posterior group, anterior group, abductor group and adductor group
Detailed annotation of all normal anatomy demonstrated on each image
The muscles of the lower back and thigh work together in keeping the hip joint stable, moving and aligned. The muscles of the hip are divided into four distinct groups based on their location. The four categories include the posterior group, anterior group, abductor group and adductor group.
Frontal plane
The anterior group of muscles features the muscles which flex the thigh at the hip joint.these anterior group of muscles include:
- The quadriceps femoris group consisting of the vastus intermedius, rectus femoris, vastus medialis, vastus lateralis
- The iliopsoas group consisting of the iliacus muscles and psoas major (Dimon & Qualter, 2008).
The posterior muscle group comprises of the muscles which extend the thigh at the hip joint. The posterior muscles groups include gluteus maximus and the hamstring group which comprises of semimimebranosus, biceps femoris and the semitendinosus muscle (Muscolino, 2010) as shown in Figure 42.

Figure 42
Sagittal plane
The groin muscles of the adductor muscle group is located at the thigh’s medial side. The adductor muscles move the thigh towards the midline of the body. The adductor group of muscles consists of the adductor longus, adductor magnus, addutctor brevis, gracilis muscles and pectineus (Wilson, 1992) as shown in Figure 43
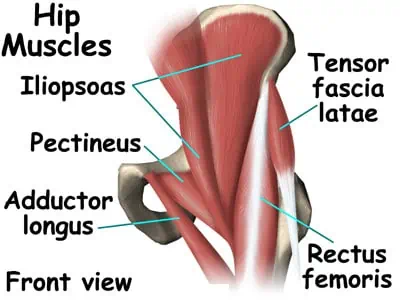
Figure 43
The abductor muscle group of the hip is located on the thigh’s lateral side and moves the thigh away from the midline of the body. These muscles include the superior gemellus, piriformis, tensor fasciae latae, inferior gemellus, gluteus medius, Sartorius and gluteus minimus muscle Brungardt et al (2006) as shown in Figure 44

Figure 44
Conclusion
In conclusion, the paper discussed ten case studies about normal anatomy of different body regions. Each case study was discussed individually where the major focus for each case study being brief justification, review and overview of the imaging protocol and image annotations. The case studies used in the paper include the skull, thoracic cage, arm skeleton, human heart, kidney anatomy, liver anatomy, stomach, muscles of the arm and hand, muscles of the leg and foot, and finally muscles of the hip
References
Agur, A. M. R., Lee, M. J., & Grant, J. C. B. (1999). Grant’s atlas of anatomy. Philadelphia: Lippincott Williams & Wilkins.
Behnke, R. S., & Donnelly, J. E. (2001). Kinetic anatomy. Champaign, IL: Human Kinetics.
Boyd, W. (2003). Any human heart: A novel. New York: A.A. Knopf.
Brenner, B. M., & Rector, F. C. (1991). The Kidney. Philadelphia: Saunders.
Brungardt, K., Brungardt, B., & Brungardt, M. (2006). The complete book of core training: The definitive resource for shaping and strengthening the “core”–the muscles of the abdomen, butt, hips, and lower back. New York: Hyperion.
Chung, C. B., & Steinbach, L. S. (2010). MRI of the upper extremity: Shoulder, elbow, wrist and hand. Philadelphia: Wolters Kluwer Health/Lippincott Williams & Wilkins.
Dimon, T., & Qualter, J. (2008). Anatomy of the moving body: A basic course in bones, muscles, and joints. Berkeley, Calif: North Atlantic Books.
Doyle, J. R., & Botte, M. J. (2003). Surgical anatomy of the hand and upper extremity. Philadelphia: Lippincott Williams & Wilkins.
Draves, D. J., & Zelichowski, J. E. (1986). Anatomy of the lower extremity. Baltimore: Williams & Wilkins.
Flynn, T. W. (1996). The thoracic spine and rib cage: Musculoskeletal evaluation and treatment. Boston: Butterworth-Heinemann.
Gadžijev, E. M., & Ravnik, D. (1996). Atlas of applied internal liver anatomy. Wien: Springer.
Glisson, F., Cunningham, A., & Wellcome Unit for the History of Medicine (University of Cambridge). (1994). From Anatomia hepatis (the anatomy of the liver), 1654. Cambridge: Wellcome Unit for the History of Medicine.
Graves, F. T. (1971). The arterial anatomy of the kidney: The basis of surgical technique. Bristol: John Wright.
Green, J. (2006). Skeleton. Mankato, Minn: Stargazer Books.
Gresczyk, E. G. (1967). Muscles of the leg and foot during walking: An electromyographic study of normal and flatfooted subjects. Kingston, Ont.
Hale, R. B., Art Students League (New York, N.Y.), & Jo-An Pictures, Ltd. (Firm). (1983). The Rib cage. New York: Jo-An Pictures.
Kenyon, C. M. P. (1989). The kinematics of the rib cage.
Kinne, R. K. H. (1989). Structure and function of the kidney. Basel: Karger.
Lapatza, C., Watters, J., Chaplin, C., & Goitiandian, E. R. (1994). The human heart. Bilbao, Spain: Near, S.A.
Larsen, C. 1997. Bioarchaeology: Interpreting Behaviour From The Human Skeleton. Cambridge: Cambridge University Press.
Liberace, R., Lubkin, A., & Liberace Studio (Firm). (2013). Anatomy : the arm and hand: With Robert Liberace. Washington, DC: Liberace Studio.
MacConaill, M. A., & Basmajian, J. V. (1969). Muscles and movements: A basis for human kinesiology. Baltimore: Williams & Wilkins Co.
Mays, S. 1999. The Archaeology of Human Bones. Glasgow: Bell & Bain Ltd.
Muscolino, J. E. (2010). The muscular system manual: The skeletal muscles of the human body. St. Louis, Mo: Mosby/Elsevier.
OpenStax CNX. (n.d.). Retrieved March 19, 2015, from http://cnx.org/contents/[email protected]:45/Anatomy_&_Physiology
Parker, S. (1989). The skeleton and movement. London: F. Watts.
Parker, S. (2004). The skeleton and muscles. Chicago, Ill: Raintree.
Parker, S., & Dowell, P. (1988). Skeleton. New York: Knopf.
Perin, R. (1983). The human heart. Buffalo, N.Y: Hallwalls.
Resnick, M. I., & Parker, M. D. (1982). Surgical anatomy of the kidney. Mount Kisco, N.Y: Futura Pub. Co.
Roberts, C. & Manchester, K. 2010. The Archaeology of Disease Third Edition. Stroud: The History Press.
Ryū, M., & Cho, A. (2009). New liver anatomy: Portal segmentation and the drainage vein. Tokyo: Springer.
Self, W. (2009). Liver: A fictional organ with a surface anatomy of four lobes. New York: Bloomsbury.
Templeton, F. E. (1964). X-ray examination of the stomach: A description of the roentgenologic anatomy, physiology, and pathology of the esophagus, stomach, and duodenum. Chicago: Univ. of Chicago Press.
White, T. & Folkens, P. 2005. The Human Bone Manual. London: Elsevier Academic Press.
Wilson, T. M. (1992). Effects of strengthening the stabilizing muscles of the hip joint on strength gain of the hamstring group.
Wolf-Heidegger, G., & Köpf-Maier, P. (2006). The color atlas of human anatomy. New York: Sterling.
With a student-centered approach, I create engaging and informative blog posts that tackle relevant topics for students. My content aims to equip students with the knowledge and tools they need to succeed academically and beyond.
by Herman Bailey | Jan 13, 2026 | Essays |
Introduction
Cisco systems is one of the earliest multi-nationals to engage in providing networking equipment. The company is currently headquartered in San Francisco but operates within more than 25 countries in the globe. Cisco first made history in the early years by designing routing software or the University of Stanford. At the time, little was known in terms of routing software and other networking mechanisms. This product catapulted the company into instant fame and drew a large target market for the still new company. The growth of Cisco was one to be reckoned with. Within a few years of establishment, majority of networking companies are still struggling to get off their fit and make a semblance of profit. The market is saturated with various companies making the same product and appealing to the same consumer. However, Cisco came into the market at a time that the global industry was yet to understand and come to terms with the complexity of the networking software. The first registered router in 1987 by Cisco more than tripled the income for the company. Within the next five years, the company would become so large that it would be sold on the public market for more than $200 million.
Cisco’s growth to date can be attributed to the fact that the company has not lost touch with the market. The company still employees’ massive talent to predict future changes in the industry and also the tastes of the consumer. Towards the beginning of the 90’s for example, the growth of the internet changes and transformed communication industry. In the past the company had relied heavily on routing devices and software for a large portion of their income. This demand of course declined drastically and this could have impacted heavily on the company perhaps even causing severe losses. However, Cisco it seems was prepared for the changes, with products such as modems access and GSR routers. With all other companies being caught unaware by the internet wave and with each of these companies struggling to finance research into viable products; Cisco immediately became a leader and not just a leader but a monopoly provider of the internet products. (Hill 2002) shows that with the beginning of the millennium, the growth of internet was astronomical. Cisco having set a place for itself at the top of the market quickly became the most sort after company. He cites, the Forbes article in February 2000 naming Cisco the most valuable company of the century with a capital of $500 billion. Less than two decades after opening its doors, the company had moved from a little known industrial company in San Francisco to a giant company drawing not just the interest of investors globally but also interest of economic and political experts.
In the year 2006, the company began focusing more on growth in the global markets. For a while, Cisco had dominated the markets at home, but was still not a household name in the global markets. Seeking to be a trend setter once again, the company began seeking to reach the average consumer by humanizing their own campaigns. Entry into the Asian region specifically into the Indian markets established the position of Cisco in the globalization markets. However, newer and other international companies have began challenging Cisco’ lucrative position as the number one network service provider. Of great concern is the presence of Alcatel- Lucent ad Huawei. Huawei has especially challenged the position of Cisco in Asian and Factors influencing job satisfaction among public sector employees: an empirical exploration. South African markets. These markets offer excellent growth opportunities because they are largely unexplored. Forbes in the year 2011, reported that a cut into the profits of the company, following a weakening hold on the markets. In fact the decline of profits forced Cisco to reduce its annual expenditure budget by at least $1billion.
Cisco has maintained a lead in the market by acquiring and maintain the talent in the industry. Perhaps the biggest and most effective acquisition came in the form of Stratacom. This is still touted as the biggest computer literacy. This will facilitate the introduction of the ICT curriculum in the college that is can be comprehended by the Dubbo teaching staff. The acquisition in the industry. The interesting thing about Cisco’s acquisitions is that they do not divert the company from its major products and services, rather the extend the nature of services and products adding value into them. They allow entry into yet unexplored markets and provide resources needed to make necessary changes in technology and quality of services being provided.
Range Of Transaction Modes
Cisco continues to be the largest provider of network solutions. Even with challengers such as Huawei, the company continues to maintain a lead in the market. When Cisco establishes subsidiaries outside their market, they move from a domestic strategy phase to international strategy phase. At the bargaining of entering the international markets, each subsidiary enjoyed relative freedom in terms of developing its own strategies and implementing the same. However, at the beginning of 2004, the company recognized that there was a serious dissociation in various subsidiaries. Consumers who entered the subsidiary do not get a similar experience in another subsidiary. As such the company sought to consolidate the transaction modes to ensure that all subsidiaries enjoy a strong market share. However, will still consolidating the service provisions; the company also ensures adaptation of products to fit the local market peculiarities.
As Cisco is growing into a recognized multi-national company, they become more and more aware of the opportunities to be gained from integrating and creating a single strategy on a global scale. The global strategy involves a carefully structured single strategy rather than haphazard strategies spread over various strategies. The single strategy spreads across the entire network of subsidiaries, encompassing many countries simultaneously and leveraging synergies across many countries. The term “simultaneous” is often used to indicate that most of the activities of the different subsidiaries are coordinated from the headquarters, in San Francisco in order to maximize global efficiency, which allows multinational firms to achieve the economies of scale and scope that are critical for global competitiveness, (Alon 2003 Venkateswaran 2012).
Moving from a domestic or international strategy into a more globalised strategy has not been an easy process and has created various strategic challenges. The main challenge has been the development of a single strategy that can be applied into varying markets all over the world, (Roffey and Morkel 2001: Rugman and Hodgetts 2003), while at the same time maintaining the flexibility to adapt that strategy to the local business environment when necessary. There are three ideal things to consider in the transaction strategy applied by the company. First is the degree of involvement and coordination from the headquarters. The different country locations are coordinated, planned and executed inter-dependently. It is notable however, that Cisco’s strategy has not been strongly coordinated and linked from the top. However, there has been significant coordination between the activities of the centre and those of the subsidiary companies. (Czinkota 1998, Adekola and Sergi 2007, Hill 2008 ) secondly standardization to the degree of product standardization and responsiveness to the local business environment. Through his system, the products, services and processes of production across the various countries of operations. According to (Newlands and Hooper 2009) the international strategy of transaction Cisco assumes that the subsidiary companies should respond to local business needs, unless of course there is a good reason as to why not. On the other hand, the global strategy as applied by Cisco should standardize its operations and products in all the different countries, unless again there is a good reason for not doing that as well. The third important aspect is in terms of the company’s competitive moves. Culpan (2002), Peng (2009) and Avadhani (2010) conclude This is the extent to which the competitive moves are inter-dependent across the various countries of operations. The Cisco strategy executes competitive battles not on a country by country basis but rather on a global scale. While still addressing the unique competition and market characteristics presented by each country, the company seeks to have a standardized strategy through which they address competition. So far, the strategy has been based on the marketing concept that is ensuring that that the company products anticipate and meet the needs of the consumer way ahead of the competition.
For Cisco’s strategy to be global it does not require absolute standardization. Many companies have failed in this aspect. In an attempt to enter a global arena, companies focus more on creating uniformity and standardization and fail to focus on the uniqueness of the different markets. The result is that survival becomes difficult in some markets and quite impossible in others. Rather as the case study featuring Cisco shows it pays for the main elements of the core strategy to be standardized, coordinated and integrated consistently across countries, with varying degrees of adaptation to local market peculiarities when required. That is, as stated by (Bickerstaffe and Dickinson 1999 ) multinational firms look for the appropriate level at which each dimension or all dimensions can be pursued. Thus Boyce (2002) and DeToni and Franco (2011) conclude that the global transaction mode is the process of designing a coherent, coordinated, integrated and unified strategy that sets the degree to which a firm globalizes its strategic transactions in different countries through standardization of sales, configuration and coordination of activities in different countries and integration of competitive moves from countries.
HISTORICAL DEVELOPMENT
Cisco’s history begins in Stanford University, where the founder Leonard Bosack was in charge of the computer science department. The professor with his colleagues first developed routers that were similar in structure and components to some that had been stolen in the university. However, both colleagues were forced to resign from Stanford after accusations of theft and fraud arose against them. They went on to register the routers under their company name, and Cisco Systems began making a name in the market. Within a year of opening its doors, the company was making millions, enough o acquire new staff and open branches in the country.
After five years, Cisco was a large enough company to go public. The decision to go public was consistent with the need to increase the capital base. The company needed a larger capital for the upcoming acquisitions. In addition, the ICT industry is renowned for many changes and in fact its own radical transformations year after year. Research and development is vital for the survival of any company. Acquisition of excellent research talent and the resources required to put the company on the right path towards development of ideal products all need excess capital. Based on this the company sold out in the public market, earning capital just shy of $250 million. Beginning the year 1992, the company began expanding and making acquisitions that would later make entry into the international and global markets easier. In the beginning, acquisitions were considered that would allow Cisco diversification into newer areas of service provision. However, research showed potential to be found in the ICT industry. On this basis, therefore Cisco sought companies that would foster growth of the company without having to diversify into new industries.
The growth of Cisco as a company has been one to be reckoned with. Cisco’s partners and subsidiaries have continued to reign in the market, leading in terms of service provision and access to quality products. The company maintains a high customer base, which is re-assured by the after service assurances granted to the customers. The Cisco Company using this strategy has managed entry into the new markets such as Asia and Africa. Here, they have introduced and explored new possibilities in networking. With an initial poor performance in African and Asian markets, Cisco’s management learnt valuable lessons. Whereas focus had centered on providing standardized products, the new markets forced the company to reconsider. During the early millennium Cisco lost a good portion of the market to competitors including Huawei. In 2004, Cisco re-entered the markets using strategies that were now structured and more suitable to the specific markets. However, the subsidiaries are still an extension of the central office and headquarters allowing only for a little maneuvering. The maneuvering allows the subsidiaries to respond actively and effectively to the challenges in the specific market. This is not the end; Cisco continues to plan for more structured investments, entry into new markets and possibilities of acquisitions.
Major Acquisitions
Majority of Cisco’s subsidiaries come in the form of acquisitions through either public purchases or private arrangements. ICT in itself is shrinking the distances and eliminating boundaries within the business itself.
Strata com: continues to be the largest acquisition in the industry to date. Stratcom made a name and drew the interest of Cisco through the ATM software. However, the only important thing to note about this acquisition was not in the ATM software but rather in the Wide Area Network (WAN) equipment. analysis shows that the project was entirely beneficial. The major areas of expenditure for the project were on transport, Acquisition of the company, allowed Cisco to take and make an impact in the business switching business. Using the company resources, Cisco entered the business of ensuring stronger networking. There have been several reports indicating increased globalization in the access of WAN services. At the top of the game of course is Cisco. Although at the time of the acquisition majority of the critics felt that Cisco did not need to add to its portfolio, with time this has proven to have been the right track for the company to take.
Cerent Corporation: Cisco actively pursued and subsequently succeeded in purchasing this company. For a long time, Cerent has maintained the lead in its own targeted market using its first product. This product is the Cerent 454. After acquisition of the company, this product was fast improved using the newly acquired talent. At the end of the year, the same product was rolled out as the Cisco 154154. Cerent, allowed entry into a new transaction level, consumers and customers could now access the product on a global and international level. Cerent continues to be the most expensive purchase of a company attempted successful by Cisco. The surprising fact was the ability of Cisco to go into such highly priced negotiations even though Cisco itself was still considered a young company. Many in fact, felt that the end of Cerent was near after the Cisco purchase. However, the company devoted many resources and much of its talent into turning Cerent from just a national to an internationally recognized company. The business unit purchased through Cerent has grown into a billion dollar unit, much feared and offering serious competition to other companies in the market.
Linksys: was acquired in 2003. This was a different company from those that Cisco frequently sought out. The main reason was because it was a small company in itself. However, it provided a unique aspect to Cisco by allowing the company entry into the home network business. Today majority of networking s carried out in homes, with even a greater majority of home networks expected in the future. The purchase of Linksys was in fact a strategic move that competitors had failed to anticipate. By gaining the home market, once again, Cisco became a number one network provider for the average consumer. With the increase in talent and resources, Cisco manufactured and brought into market the Cisco Valet, a product that remains unequaled in the ICT market.
PATTERNS OF INTERNATIONALIZATION
Wibbeka (2009) and John (1997) define internationalization as the increased presence of a company within international operations. Ideally the patterns of internationalization take three forms that is the U model, the I model and finally the network approach. Cisco has advanced and directed the internationalization process more towards the U-model. The idea is to increase the level of knowledge with regard to processes while at the same time reconsidering the commitment of various resources. According to (Martin and Chaney 2006) a firm in the u model also known as the process model, begins by exporting products directly to a particular range of countries, this is then followed by exportation through independent producers within the country and finally, see tin up of a manufacturing company within the country. Looking into the establishment of Cisco manufacturing and distribution centers, one gathers that Cisco’s expansion is not only directed but seemingly structured into this model. Countries of operations are groups according to their similarities and challenges they offer the company.
Group one: consists of Europe, Middle East, Africa and Russia. These countries may seem to lack any common ground. However, their similarities arise in the fact that they do not possess a manufacturing unit but rather more of distribution centers. The countries though far from each other in terms of economic growth have each provided a unique opportunity for growth. They possess resources that indeed bring down the cost of distribution including labor. However, they also pose a challenge in terms of lax markets, with low demands on products.
Group two: Asia, Japan and china: these countries have seen the greatest progress in terms of technology. Each of them enjoy a full processing plant within their borders. Such processing factories, research and development centers have been equipped with fast growing and creative talent. Entry into these countries has however been challenged by increased saturation of other ICT companies.
Group three: America, Canada and Latin America: this countries have provided the base upon which Cisco has grown. Here, the company enjoys large, loyal customer base. There is little challenge from competitors but it is not as widely felt as the countries in group one. Further, the company is highly recognized in these countries, where it attracts not just a large portion of the market but also a wide network of talents.
COMPANY GOALS FOR INTERNATIONAL BUSINESS
Expand markets and increase sales:
There is a general belief that there are several ICT markets in the globe, all converging around the world. These markets provide an ideal opportunity for growth. The increase of Gross National Product in the developed markets while providing an ideal opportunity for incoming expenditure also provides the challenge of increased competition. With majority of the international markets becoming more saturated, the company seeks new opportunities for growth and expansion. According to (Kotabe and Helsen 1998), The convergence of markets allows a customer in America and one in Africa to enjoy the same quality of products. In the ICT industry, there of evidence that the customer tastes and preferences are converging globally. The internet has allowed access to knowledge, while at the same time social media has brought convergence in customer culture. In this arena, the world is quickly becoming a single market. Companies that have considered and entered the market before will therefore enjoy a stronger position.
Controlling of costs
For the past decade, Cisco has become concerned with increased costs of production. This coupled with challenges brought on by competitor’s lowered prices for similar products have forced the company to reconsider the expenditure account. One key factor that has influenced the entry of the company into the global arena is the global scale economies. Whereas some countries such as the developed countries, costs of production maybe high due to increased costs of labor and other factors; in others such as the Asian markets, the same costs are driven down by readily available labor at much lower costs. (Thomas and Inkson 2003 and Hill 2005) state that economies of scale occur when a product or a process can be performed more cheaply at greater volumes than at lesser volumes. Products offered by Cisco are standardized across the countries; this means increased volume of production lowers the cost of production. In the industry it has become quite difficult for multi-nationals to differentiate themselves and cost becomes key in achieving and sustaining a competitive advantage.
The cost of the production process has a strong impact on the profits being recorded in the company. With more and more companies entering the market, the lower the cost the higher the profits recorded. With concern for resources directed at production increasing, there is need for the company to seek newer resources. In an effort to identify the lowest cost of resources, the company has entered the global markets. International markets are not only targets for the finished products. More often than not, companies tend to settle in markets where they can also access vital resources including unique talent, (Bjerke 1999). According to (Lan 2005, Hockley 2010) Governments attempting to encourage investment in their countries pass laws with attractive tax returns and percentages, cheap labor costs and cheap technology. The relationship is therefore mutual; on the one hand the companies enjoy lowered costs of production and access to cheap resources. On the other hand, the governments increase the employment rates and income circulation in the country. This has proven efficient in attracting companies such as Cisco who are seeking lower costs of production.
Diversification
The entry of the internet has forced majority of the companies to consider diversification into various other lines of production. Cisco for example had for a while remained a string company rooted on networking businesses. Recent changes in the tastes and demands of the consumers however, have led the company into new products and especially those designed for mobile devices and also home networks. The product differentiation is an attempt by the company to reduce the risk it takes in introducing and entering new markets. The company has maintained a strong foothold in the American markets. However, recent fluctuations in the prices coupled with the recent economic crisis led the company to consider diversification of products. Each country has proved to have specific needs which can be addressed using newer and more identified products. The result is that the company is likely to enjoy an increase in profits with less fluctuations on the same. (Elashwami and Harris 1998, Condon 2002 ) raised concern with regard to this strategy, citing that the company would be forced to commit more of their profits and capital towards research and development of the new products. Further, such products are likely to draw the interest of the company from the original services for which they are renowned for. The result is that failure and weakening of the company structure would imminent. (Hoffman 1994) countered that such costs including the capital expenditure would be well worth it, if proper research is carried out onto the right product. With the right product, addressing the specific gap in the market, profits would increase exponentially. This is especially the case if such products are differentiated within the same line rather than diverse products in various industries. Maintaining diversification within the same industry allows for similar diversification of the costs of production.
ORGANIZATIONAL STRUCTURE
Cisco’s global management structure is one to be reckoned with. The structure includes a CEO at the top of the company. The CEO is selected by a board and voted on by the shareholders. Each CEO has specific performance requirements which they must adhere to. It is to be noted however, that unlike many multi-nationals Cisco’s CEO does not enjoy much freedom. Decisions are frequently regulated and tested before being out in place. This is perhaps why not much change has been made in each tenure, with each and every CEO. Not a singular change can be traced back to a particular CEO. Changes are more gradual than sudden. From the CEO, there are various executives in charge of the different departments and subsidiaries. (Trompenaars 1994, Stonehouse 2004) criticize the stand of Cisco with regard to the selection of executives running subsidiaries. The company has become renowned for importing their own talent from the headquarters to run subsidiaries as opposed to finding local talent and training them. From the executives, the company becomes more lenient in the selection of the business managers. The business managers are in direct contact with the consumers running direct lines of production, distribution and even after sales care. The standardization dimension expressed by () defines the global management as offering similar products through a similar structure in the company. However, for this strategy to continue being beneficial, the company needs to identify and make minor adaptations to local peculiarities. The company integrates the needs of the market with the organizational structure. For example within the Asian markets, much focus has been grated towards identification of local innovations which lead to improvement of Cisco products. With recognition of such products as having been locally sources, the market has become more receptive of the company.
(Wolfe 1999) shows that addressing the peculiar needs of the market through the organizational structure may pose some slight challenges. The challenges include identification of ideal talent, human resources that not only understand the products and services but also the standardization measures set by the company. (Mole 2003) identifies a similar challenge, where the company may find ideal human resources on the ground but then such resources fail to capture the nature and need for standardization as set by the company.
Human resource management
(Wood 2006) indicates that multi-nationals fall into three major categories and these are: the first who select executives and majority of the managers from the home country; the second who consider employees only from the parent company home and the host country and finally a third category who take on a more international perspective and consider employees from any nationality. Cisco surprisingly seems to fall in the first category. (Laurie 2001) cited executives of the company defending the chosen strategy of relying on executives from the home country, despite presence of talented executives in the host country. The idea is that these executives are able to transfer the strategy that has worked for the company with fewer challenges. They have already mastered such challenges, can expect them and address them effectively. Further, this system has paid off in terms of offering challenging opportunities for executives back at home which in turn increases productivity.
However, the company has recently recorded growing concern of difficulty in entry to some international markets. Consumers are not responding to marketing and advertising strategies simply because they feel that the company has no interest in growing local talent. The result is that the company is re-structuring in an attempt to move more towards an international outlook. However such a policy can be proven to be quite expensive, in addition such strategy would take a long time to implement. The ideal idea would be to move more towards a combination of home and host country labor especially in the managerial positions. This is a useful strategy especially where local firms have been acquired by the company. Hiring locals eliminates various challenges such as language barriers, expensive training methods because they have acquired the right skills and problems brought on by adjustment of the managers and their families. Relocation of executives from their home countries often posses the problems of adjustment and proves to be costly to the company as they attempt to make settlement easier.
Ethnocentrism versus geo-centrism
Cisco is one company that can be considered purely ethnocentric in nature. The strategy began in the early years of internationalization. At the time, Cisco was unaware and unable to access the local talents to head subsidiaries. However, over time, the strategy has taken root commanding the human resource and executive recruitment policies. (Blenkhorn and Fleisher 2005) states that Ethnocentrism may seem like an offhand disadvantaged system to the naked eye. However, it possess some benefits top among them being that subsidiaries require very little supervision in the early stages of setting up. This is because those in charge are aware of, and equipped to handle each and everything as per the company regulations. (Mullins 2005) concurs by stating that many would prefer the company to head into a geo-centric view. However, such view can be quite expensive for the company to set up. Further with a geo-centric view, the new subsidiaries take much longer to become productive, as executives and personnel are undertaken through training and orientation. Should such a company face a challenge in this early stages, chances of losses are imminent because the staff is unaware on how to react to the challenges.
That being said, the challenges out forward by the market in terms of lack of support for subsidiaries, have forced the company to consider a change, albeit a slow one towards a more geo-centric view. This can be seen by the hiring of newer executives in the past two years, many of which are locally recognized. (Rudani 2011) highlights that companies such as Cisco are coming to the realization that the skills required to fulfill the same job differ from one location to another and the candidates are almost always affected greatly by the local culture and physical environment. With this in mind, there is a desire to integrate both ethno-centrism and geo-centrism and find or strike a balance.
Organizational control
Cisco is a wholly owned investment, where the parent company can shape the strategic direction of the subsidiaries, (Mullins 2005) cites that insufficient control can a limit a firm’s ability to align the strategic direction of the partnership with its own strategy, and it can limit a firm’s ability to protect its interests in the partnership. There are two types of control that are exercised in Cisco and these are: strategic control and operational control.
As stated by (Rao 2001) strategic control is control over means and methods on which the conduct of the whole company depends for example control over how the capital is utilized, the setting of priorities and even the hiring of senior executives. On the other hand, operational control as defined by (Erskine 1991) is control over the process of production within the company, in the sense of determining how the employees of an organization perform their work, for example control of purchasing and quality control in the subsidiary branches. For the past few years, Cisco’s organization control has been heavily influenced by the strategic priorities. The firm has prioritized customer satisfaction coupled with reductions of costs. However, with each subsidiary culture and existing knowledge have influenced the approach to organizational culture.
CONCLUSIONS
Understanding the motives behind a firm’s decision to internationalize its business activities helps to explain why and how such a firm engages in international business activities. Cisco for example was compelled to make its first international move following the growing demand for ICT, and the increased availability of the internet and online market. Companies often decide to internationalize without fully investing in a foreign location. However, a foreign investment is often considered much riskier and even more expensive. According to (Dunning 1997) there are four main reasons for such a move: natural resource seeking, market seeking, efficiency seeking and strategy seeking. (Schmidheiny 1992) states that majority of the companies begin the internationalization foreign investment with purposes of seeking new markets. However, as the process grows other reasons come into play. For example, Cisco’s movement into Canada and Latin America was purely to seek new opportunities for growth. On the other hand, over time the internationalization has taken a more efficiency prone aspect. The company has expanded with the main motive of finding cheaper resources through which the expenditure account can be cut down and in turn profits margin can be increased.
(Parhizgar 2002) through research has proven that first entrants into a market often enjoy a greater share and more stability than latter entrants. For instance Cisco has been able to reap considerable benefits and first mover advantages by expanding into Russia in the early 90’s. At this time, the competitors of the company had not even begun considering such a move. The entry into Russia allowed the company to gain footing as the leader in network and router manufacturing. In addition, Cisco enjoyed the advantage of obtaining new technology from Russian and American government support raising majority of the barriers that late comers have had to endure. However, this is not the only reason why Cisco has engaged in internationalization, the attractiveness of countries where business has been launched is also vital. (Sen 2002) states that the country’s host market must be desirable for business to encourage such a move. Cisco could be attracted because of the host country’s market size and potential. For example, the decision to enter India was based on the probability of growth as the country offers a high potential for income generation. In addition, the market also offers cheap labor and highly skilled workers which can greatly push the company into the next age technology.
All types of firms, multi-national, single country, small or large business need to undertake operational renewal constantly in order to regain control in those parts of the organization that are ageing and becoming uncontrolled. However, the Cisco study demonstrates that the control management cannot be easy when the firm is multi-national. Control becomes more complex and involves more stakeholders than just the local headquarters. (Millet and Wiesner 2000) cites that multi-nationals operate across several countries, which creates a complex and sometimes chaotic mix of management practices influenced by different national cultures and institutions. (Murray et al 2006) further indicates that some subsidiaries are more aware of the dynamics of the business environment and culture within their location and therefore are more likely to resist measures of control. In addition the attitude of the people with regard to control measures put in place by the company are also affected by a set of culture specific factors, norms and values which therefore adds another layer of complexity to control management. The different behaviors and attitudes of employees towards control management at subsidiary levels increase the potential for conflict between the centre and subsidiaries and may hinder the success of any strategy chosen by the company.
REFERENCES
Adekola, A., & Sergi, B. S. (2007). Global Business Management A Cross-Cultural Perspective. Aldershot, England, Ashgate
Alon, I. (2002). Chinese Culture, Organizational Behavior, And International Business Management. Westport, Ct, Praeger.
Avadhani, V. A. (2010). Global Business. Mumbai [India], Himalaya Pub. House.
Bickerstaffe, G., & Dickson, T. (1999). Mastering Global Business: The Complete Mba Companion In Global Business. London, Financial Times.
Bjerke, B. (1999). Business Leadership And Culture National Management Styles In The Global Economy. Cheltenham, Uk, Edward Elgar
Blenkhorn, D. L., & Fleisher, C. S. (2005). Competitive Intelligence And Global Business. Westport, Ct, Praeger Publishers.
Boyce, G. (2002). Co-Operative Structures In Global Business Communicating, Transferring Knowledge And Learning Across The Corporate Frontier. Quorum Books
Condon, B. J. (2002). Nafta, Wto, And Global Business Strategy How Aids, Trade, And Terrorism Affect Our Economic Future. Westport, Conn, Quorum Books.
Culpan, R. (2002). Global Business Alliances Theory And Practice. Westport, Conn, Quorum Books.
Czinkota, M. R. (1998). Global Business. Fort Worth, Dryden Press.
De Toni, A. F., & Franco, R. D. (2011). International Operations Management Lessons In Global Business. Farnham, Gower.
Dunning, J. H. (1997). Alliance Capitalism And Global Business. New York, Routledge.
Elashmawi, F., Harris, P. R., & Elashmawi, F. (1998). Multicultural Management 2000: Essential culture shock upon arriving in the United States. These students must understand the Cultural Insights For Global Business Success. Houston, Tex, Gulf Pub
Erskine, R. (1991). Business Management. Prentice Hall.
Hill, B. (2002). Cisco The Complete Reference. New York, Mcgraw Hill/Osborne.
Hill, C. W. L. (2005). International Business: Competing In The Global Marketplace. Boston, Mcgraw-Hill/Irwin.
Hill, C. W. L. (2008). Global Business Today. Boston, Mcgraw-Hill Irwin.
Hockley, L. R. (2010). Global Operations Management. New York, Nova Science Publishers
Hoffman, W. M. (1994).Emerging Global Business Ethics. Westport, Conn, Quorum Books
John, R. (1997). Global Business Strategy. London, International Thomson Business Press.
Kotabe, M., & Helsen, K. (1998). Global Marketing Management. New York, J. Wiley.
Lan, Y.-C. (2005). Global Information Society Operating Information Systems In A Dynamic Global Business Environment. Hershey, Pa, Idea Group Pub.
Laurie, D. (2001). From Battlefield To Boardroom: Winning Management Strategies For Today’s Global Business. New York, Palgrave.
Martin, J. S., & Chaney, L. H. (2006). Global Business Etiquette: A Guide To International Communication And Customs. Westport, Conn, Praeger.
Millett, B., & Wiesner, R. (2000). Management And Organisational Behaviour: Contemporary Challenges And Future Directions. Milton, Qld, John Wiley & Sons.
Mole, J. (2003). Mind Your Manners Managing Business Cultures In The New Global Europe. London, Nicholas Brealey Pub
Mullins, L. J. (2005). Management And Organisational Behaviour. Harlow, England, Prentice Hall/Financial Times.
Murray, P., Murray, P., Poole, D., & Jones, G. (2006). Contemporary Issues In Management And Organisational Behaviour. South Melbourne, Vic, Thomson Learning
Newlands, D. J., & Hooper, M. J. (2009). The Global Business Handbook The Eight Dimensions Of International Management. Farnham, Surrey, England, Gower.
Parhizgar, K. D. (2002). Multicultural Behavior And Global Business Environments. New York, N.Y., International Business Press.
Peng, M. W. (2009). Global Business. Mason, Oh, South-Western Cengage Learning.
Rao, P. (2010). Management And Organisational Behaviour. Mumbia, Himalaya
Roffey, B., & Morkel, A. (2001). International Business Management. Darwin, N.T., Northern Territory University Press.
Rudani, R. B. (2011). Management And Organisational Behaviour. New Delhi, Tata Mcgraw-Hill.
Rugman, A. M., & Hodgetts, R. M. (2003). International Business. Harlow, England, Prentice Hall/Financial Times.
Schmidheiny, S. (1992). Changing Course: A Global Business Perspective On Development And The Environment. Cambridge, Mass, Mit Press.
Sen, M. (2008). Business Management. Jaipur, India, Oxford Book Co.
Stonehouse, G. (2004). Global And Transnational Business Strategy And Management. Chichester, West Sussex, England, Wiley.
Thomas, D. C., & Inkson, K. (2003). health care, cultural factors have a strong influence on patients’ and families” decisions. Some Cultural Intelligence People Skills For Global Business. San Francisco, Calif, Berrett-Koehler.
Trompenaars, A. (1994). Riding The Waves Of Culture: Understanding Diversity In Global Business. Burr Ridge, Ill, Irwin Professional Pub.
Wibbeke, E. (2009). Global Business Leadership. Oxford, Butterworth-Heinemann.
Wolfe, J. A. (1999). The Global Business Game: A Strategic Management And International Business Simulation : Player’s Manual. Cincinnati, Oh, South-Western College.
Wood, D. J. (2006). Global Business Citizenship A Transformative Framework For Ethics And Sustainable Capitalism. Armonk, N.Y., M.E. Sharpe, Inc.
Venkateswaran, N. (2012). International Business Management. New Delhi, New Age International.
With a student-centered approach, I create engaging and informative blog posts that tackle relevant topics for students. My content aims to equip students with the knowledge and tools they need to succeed academically and beyond.